OTA-Key:无线密钥管理,实现灵活可靠的物联网设备配置
IF 5.4
2区 计算机科学
Q1 COMPUTER SCIENCE, INFORMATION SYSTEMS
IEEE Transactions on Network and Service Management
Pub Date : 2024-12-11
DOI:10.1109/TNSM.2024.3515212
引用次数: 0
摘要
随着物联网(IoT)行业的发展,保护物联网设备的必要性变得越来越重要。目前业界和学术界的做法都主张通过安装密钥来增强设备安全性。然而,据观察,在实践中,物联网供应商经常为批量设备分配共享密钥。这种做法可能会使设备暴露于风险之中,例如攻击者窃取数据或大规模的分布式拒绝服务(DDoS)攻击。为了解决这个问题,我们的直觉是为每个设备分配一个唯一的密钥。不幸的是,这种策略在物联网环境中被证明是非常复杂的,因为现有的密钥通常是硬编码到固件中,需要为每个设备创建定制的固件。此外,设备密钥与各自设备的正确配对至关重要。这种配对过程中的错误将需要大量的人力和时间资源来纠正,并且需要物联网供应商、设备制造商和云平台之间进行广泛的沟通,从而导致巨大的通信开销。为了克服这些挑战,我们提出了OTA-Key方案。这种方法从根本上将设备密钥与存储在闪存中的固件特性分离开来,利用中间服务器在两个不同的阶段分配唯一的设备密钥并更新密钥。我们使用ProVerif对我们的方案进行了正式的安全验证,并通过一系列评估来评估其性能。结果表明,该方案是安全的,可以有效地管理设备唯一密钥的大规模分发和更新。此外,与其他方案相比,它实现了更低的更新时间和数据传输量。本文章由计算机程序翻译,如有差异,请以英文原文为准。
OTA-Key: Over-the-Air Key Management for Flexible and Reliable IoT Device Provision
As the Internet of Things (IoT) industry advances, the imperative to secure IoT devices has become increasingly critical. Current practices in both industry and academia advocate for the enhancement of device security through key installation. However, it has been observed that, in practice, IoT vendors frequently assign shared keys to batches of devices. This practice can expose devices to risks, such as data theft by attackers or large-scale Distributed Denial of Service (DDoS) attacks. To address this issue, our intuition is to assign a unique key to each device. Unfortunately, this strategy proves to be highly complex within the IoT context, as existing keys are typically hardcoded into the firmware, necessitating the creation of bespoke firmware for each device. Furthermore, correct pairing of device keys with their respective devices is crucial. Errors in this pairing process would incur substantial human and temporal resources to rectify and require extensive communication between IoT vendors, device manufacturers, and cloud platforms, leading to significant communication overhead. To overcome these challenges, we propose the OTA-Key scheme. This approach fundamentally decouples device keys from the firmware features stored in flash memory, utilizing an intermediary server to allocate unique device keys in two distinct stages and update keys. We conducted a formal security verification of our scheme using ProVerif and assessed its performance through a series of evaluations. The results demonstrate that our scheme is secure and effectively manages the large-scale distribution and updating of unique device keys. Additionally, it achieves significantly lower update times and data transfer volumes compared to other schemes.
求助全文
通过发布文献求助,成功后即可免费获取论文全文。
去求助
来源期刊
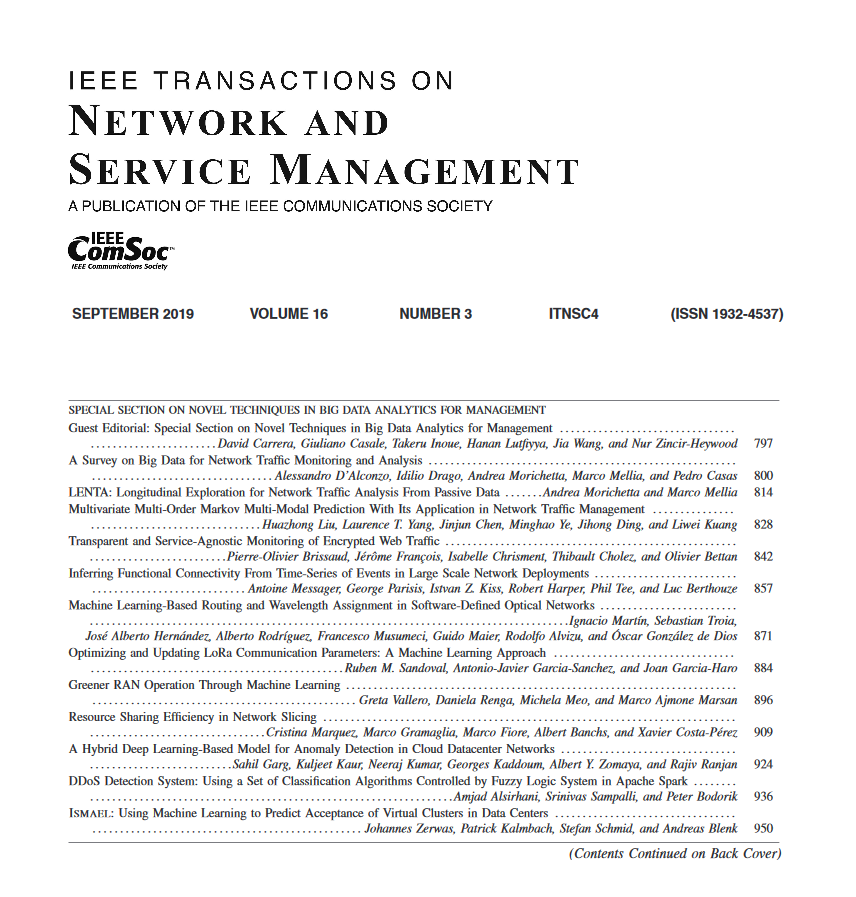
IEEE Transactions on Network and Service Management
Computer Science-Computer Networks and Communications
CiteScore
9.30
自引率
15.10%
发文量
325
期刊介绍:
IEEE Transactions on Network and Service Management will publish (online only) peerreviewed archival quality papers that advance the state-of-the-art and practical applications of network and service management. Theoretical research contributions (presenting new concepts and techniques) and applied contributions (reporting on experiences and experiments with actual systems) will be encouraged. These transactions will focus on the key technical issues related to: Management Models, Architectures and Frameworks; Service Provisioning, Reliability and Quality Assurance; Management Functions; Enabling Technologies; Information and Communication Models; Policies; Applications and Case Studies; Emerging Technologies and Standards.
 求助内容:
求助内容: 应助结果提醒方式:
应助结果提醒方式:


