基于动态扩展架构的类增量式网站指纹攻击
IF 5.4
2区 计算机科学
Q1 COMPUTER SCIENCE, INFORMATION SYSTEMS
IEEE Transactions on Network and Service Management
Pub Date : 2025-02-20
DOI:10.1109/TNSM.2025.3538895
引用次数: 0
摘要
匿名网络上的加密流量仍有遭受网站指纹(WF)攻击的风险。这种攻击会严重威胁匿名网络(如 Tor)用户的在线隐私。虽然基于深度学习的 WF 攻击在受控实验环境中实现了很高的准确性,但它们在部署后无法持续学习。在现实环境中,新网站不断涌现,这就要求攻击者不断扩大监控范围。这就要求攻击模型能够持续学习并扩展分类能力。在本文中,我们将探讨攻击者如何利用增量类学习技术来不断学习新的类,同时保留区分旧类的能力。这种方法可以缓解动态开放世界场景中的灾难性遗忘问题。我们介绍了一种新的 WF 攻击--类增量指纹(CIF),它采用了一种可扩展架构,能在资源有限的情况下实现类增量学习(CIL)。我们在各种场景中对这种攻击进行了评估,例如在 5 个和 10 个增量任务中学习 100 个、200 个和 500 个受监控的网站类别,平均准确率达到 97.8% 及以上。此外,我们还评估了 CIF 攻击在开放世界多分类场景中的有效性,并使用所提出的数据增强方法 Mixtam 在少数几个场景中对其进行了测试,在每个类别只有 30 个样本的情况下实现了 87.6% 及以上的平均任务准确率。本文章由计算机程序翻译,如有差异,请以英文原文为准。
Class Incremental Website Fingerprinting Attack Based on Dynamic Expansion Architecture
Encrypted traffic on anonymizing networks is still at risk of being exposed to the Website Fingerprinting (WF) attack. This attack can seriously threaten the online privacy of users of anonymity networks such as Tor. While deep-learning-based WF attacks achieve high accuracy in controlled experimental settings, they cannot continuously learn after deployment. In real-world environments, new websites are constantly emerging, requiring attackers to expand their monitoring scope continuously. This necessitates attack models capable of continuous learning and expanding classification capabilities. In this paper, we explore how attackers can leverage incremental class learning techniques to continuously learn new classes while retaining the ability to distinguish old ones. This approach mitigates the catastrophic forgetting problem in dynamic, open-world scenarios. We introduce a new WF attack, Class Incremental Fingerprinting (CIF), which employs a scalable architecture enabling Class Incremental Learning (CIL) with limited resources. We evaluate this attack in various scenarios, such as learning 100, 200, and 500 monitored website classes across 5 and 10 incremental tasks, achieving an average accuracy of 97.8% and above. Additionally, we assess the CIF attack’s effectiveness in open-world multi-classification scenarios and test it in few-shot settings using the proposed data augmentation method, Mixtam, achieving an average task accuracy of 87.6% and above with only 30 samples per class.
求助全文
通过发布文献求助,成功后即可免费获取论文全文。
去求助
来源期刊
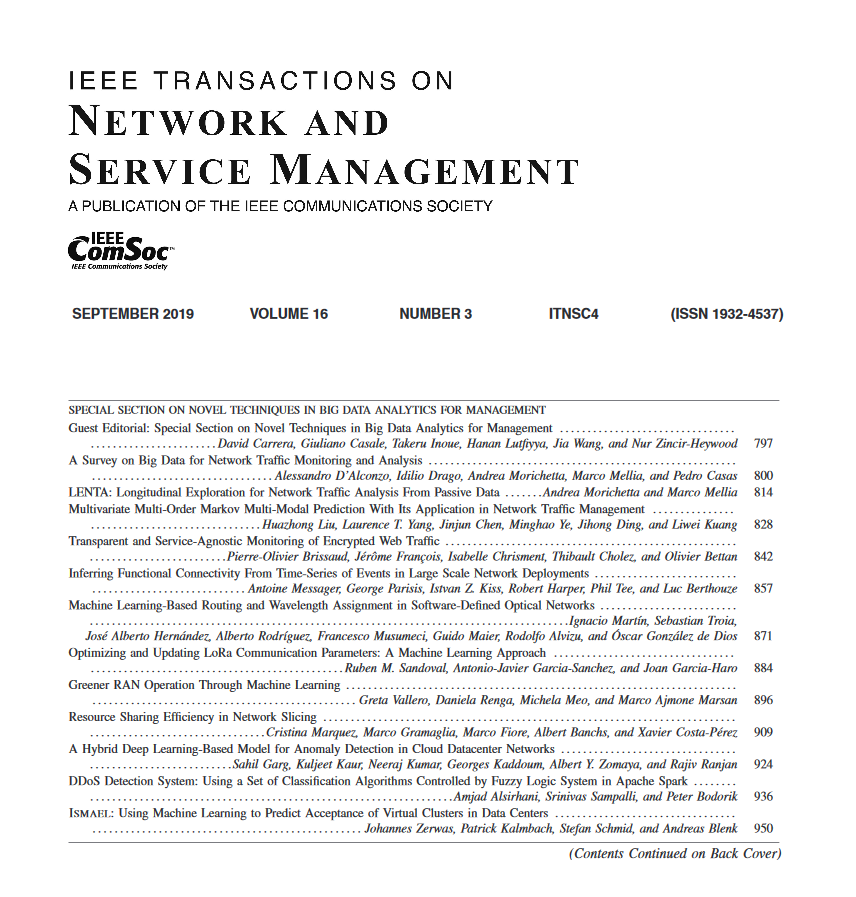
IEEE Transactions on Network and Service Management
Computer Science-Computer Networks and Communications
CiteScore
9.30
自引率
15.10%
发文量
325
期刊介绍:
IEEE Transactions on Network and Service Management will publish (online only) peerreviewed archival quality papers that advance the state-of-the-art and practical applications of network and service management. Theoretical research contributions (presenting new concepts and techniques) and applied contributions (reporting on experiences and experiments with actual systems) will be encouraged. These transactions will focus on the key technical issues related to: Management Models, Architectures and Frameworks; Service Provisioning, Reliability and Quality Assurance; Management Functions; Enabling Technologies; Information and Communication Models; Policies; Applications and Case Studies; Emerging Technologies and Standards.
 求助内容:
求助内容: 应助结果提醒方式:
应助结果提醒方式:


