用于检测分布式网络攻击的微流独立特征的重要性分析
IF 4.7
2区 计算机科学
Q1 COMPUTER SCIENCE, INFORMATION SYSTEMS
IEEE Transactions on Network and Service Management
Pub Date : 2024-09-13
DOI:10.1109/TNSM.2024.3460082
引用次数: 0
摘要
网络基础设施至关重要,因此会受到针对其操作和所提供服务可用性的有害攻击。考虑到检测率、反应时间和可伸缩性,检测此类攻击,特别是在高性能网络中,是一项具有挑战性的工作。未来的网络将面临越来越高的数据速率和流量,对攻击检测的要求也越来越高。我们彻底评估了eMinD,这是一种可以很好地扩展到高数据速率和大量数据流的方法。eMinD调查聚合的交通数据,也就是说,它不是基于微流及其固有的可扩展性问题。我们用真实世界的交通数据评估了eMinD,并将其与相关工作进行了比较,结果表明,eMinD在反应时间、可扩展性和检测性能方面优于基于微流的方法。我们将所需的状态空间减少了99.97%。平均反应时间减少了90%,而检测性能甚至有所提高,尽管高度聚合到达的流量。我们进一步展示了微流总体流量特征的重要性,例如,IP地址和端口分布,用于检测分布式网络攻击,即DDoS攻击和端口扫描。本文章由计算机程序翻译,如有差异,请以英文原文为准。
Importance Analysis of Micro-Flow Independent Features for Detecting Distributed Network Attacks
Network infrastructures are critical and, therefore, subject to harmful attacks against their operation and the availability of their provided services. Detecting such attacks, especially in high-performance networks, is challenging considering the detection rate, reaction time, and scalability. Attack detection becomes even more demanding concerning networks of the future facing increasing data rates and flow counts. We thoroughly evaluate eMinD, an approach that scales well to high data rates and large amounts of data flows. eMinD investigates aggregated traffic data, i.e., it is not based on micro-flows and their inherent scalability problems. We evaluate eMinD with real-world traffic data, compare it to related work, and show that eMinD outperforms micro-flow-based approaches regarding the reaction time, scalability, and the detection performance. We reduce required state space by 99.97%. The average reaction time is reduced by 90%, while the detection performance is even increased, although highly aggregating arriving traffic. We further show the importance of micro-flow-overarching traffic features, e.g., IP address and port distributions, for detecting distributed network attacks, i.e., DDoS attacks and port scans.
求助全文
通过发布文献求助,成功后即可免费获取论文全文。
去求助
来源期刊
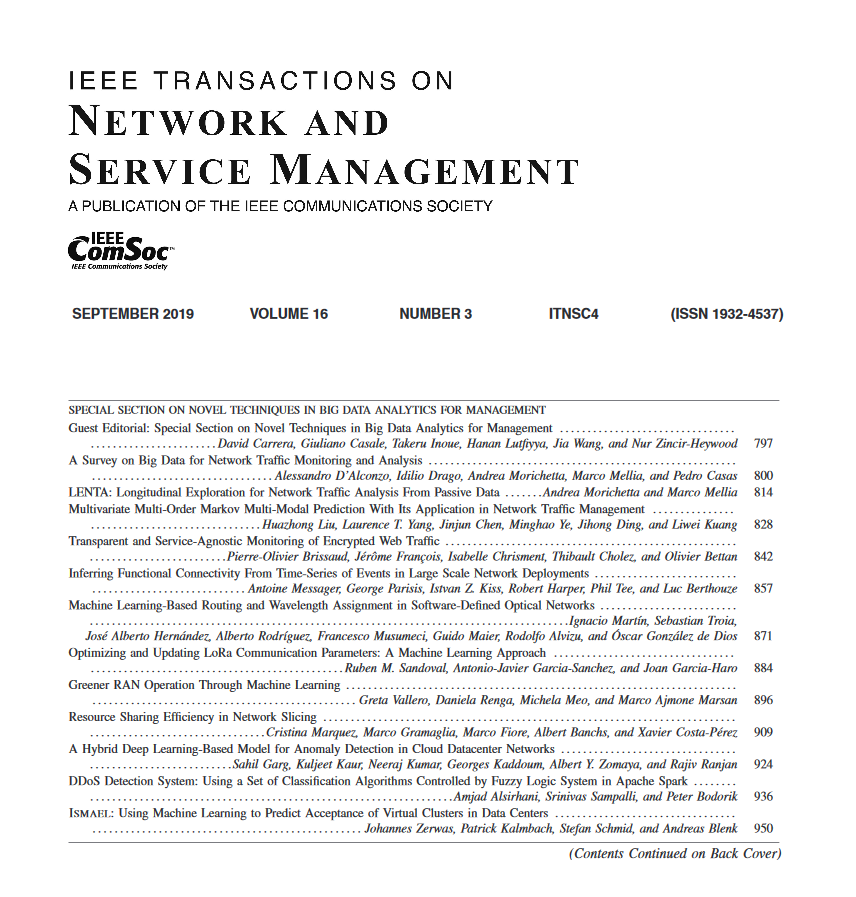
IEEE Transactions on Network and Service Management
Computer Science-Computer Networks and Communications
CiteScore
9.30
自引率
15.10%
发文量
325
期刊介绍:
IEEE Transactions on Network and Service Management will publish (online only) peerreviewed archival quality papers that advance the state-of-the-art and practical applications of network and service management. Theoretical research contributions (presenting new concepts and techniques) and applied contributions (reporting on experiences and experiments with actual systems) will be encouraged. These transactions will focus on the key technical issues related to: Management Models, Architectures and Frameworks; Service Provisioning, Reliability and Quality Assurance; Management Functions; Enabling Technologies; Information and Communication Models; Policies; Applications and Case Studies; Emerging Technologies and Standards.
 求助内容:
求助内容: 应助结果提醒方式:
应助结果提醒方式:


