SIM:通过将 "自私战略 "融入 "无辜采矿 "实现高利润
IF 4.7
2区 计算机科学
Q1 COMPUTER SCIENCE, INFORMATION SYSTEMS
IEEE Transactions on Network and Service Management
Pub Date : 2024-07-29
DOI:10.1109/TNSM.2024.3435869
引用次数: 0
摘要
自私挖矿是比特币中最著名的攻击之一,它涉及到一个自私的矿工将发现的区块隐瞒起来,并在适当的时候广播它们,以获得比诚实挖矿更高的奖励。然而,自私挖掘及其变体依赖于两个假设:攻击者仅在受害者池内进行渗透挖掘(攻击假设)和系统在完美的网络环境中运行(网络假设)。在本文中,我们提出了一种新的攻击,称为“自私的无辜采矿”(SIM)。SIM在不增加攻击者计算能力的前提下,将自私挖掘纳入传统的无害挖掘和渗透挖掘框架,扩大了攻击者的行为范围。首先,我们利用马尔可夫链分析了系统中链的所有可能状态及其在SIM攻击背景下的转移概率。我们确定了攻击者在一个受害者池、多个受害者池中的奖励,以及不同情况下的矿工困境。随后,我们研究了不完美的网络环境对SIM框架内攻击者奖励的影响,重点关注无意分叉率对奖励的影响。我们的定量分析表明,在不同的网络环境下,攻击者在SIM中的奖励分别超过了在功率调整预扣(PAW)中的奖励1.9倍和2.7倍。与其他基准相比,攻击者的奖励阈值降低到12.38%。本文章由计算机程序翻译,如有差异,请以英文原文为准。
SIM: Achieving High Profit Through Integration of Selfish Strategy Into Innocent Mining
Selfish mining, one of the most renowned attack in Bitcoin, involves a selfish miner withholding discovered blocks and broadcasting them at an opportune moment to gain higher rewards than honest mining. However, selfish mining and its variants rely on two assumptions: the attacker solely engages in infiltration mining within the victim pool (attack assumption) and the system operates in a perfect network environment (network assumption). In this paper, we propose a novel attack called Selfish in Innocent Mining (SIM). SIM expands the range of attacker’s behaviors by incorporating selfish mining into the traditional framework of innocent and infiltration mining, without increasing the attacker’s computational power. Initially, we analyze all possible states of chains in the system and their transition probabilities in the context of the SIM attack using Markov Chain. We determine the attacker’s rewards in one victim pool, multiple victim pools, and the miner’s dilemma within different cases. Subsequently, we examine the impact of an imperfect network environment on the attacker’s rewards within the SIM framework, focusing on the influence of unintentional fork rates on rewards. Our quantitative analysis demonstrates that the attacker’s rewards in SIM exceed those in power-adjusting withholding (PAW) by
$1.9\times $
and
$2.7\times $
in different network environments, respectively. The attacker’s rewards threshold reduced to 12.38% compared to other benchmarks.
求助全文
通过发布文献求助,成功后即可免费获取论文全文。
去求助
来源期刊
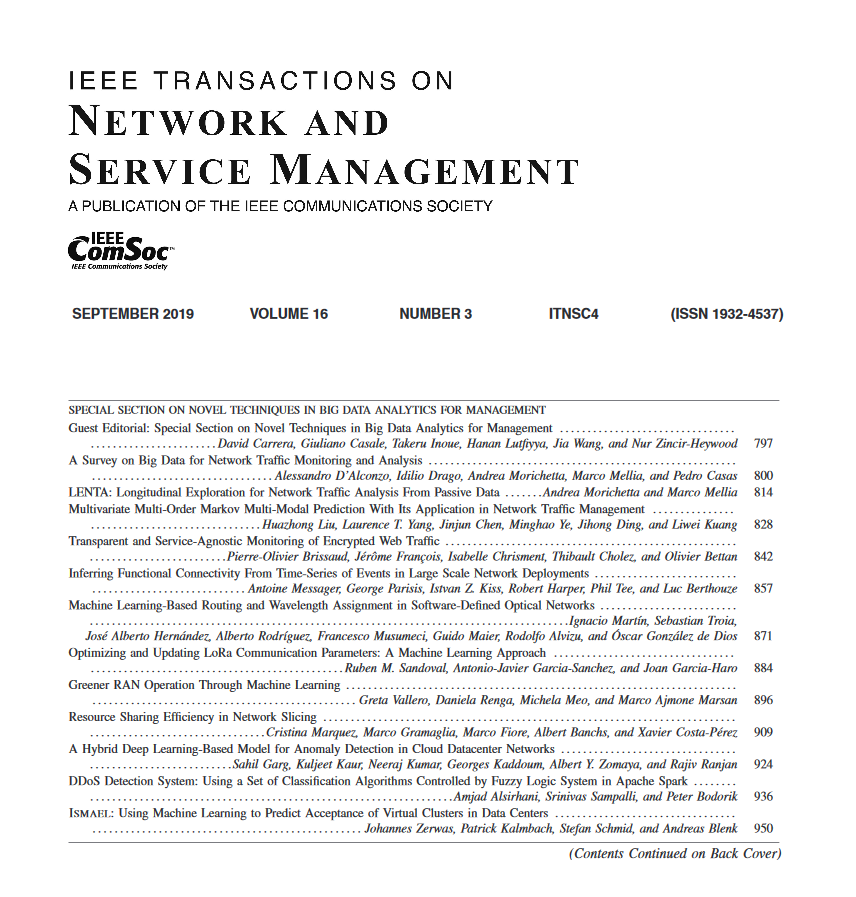
IEEE Transactions on Network and Service Management
Computer Science-Computer Networks and Communications
CiteScore
9.30
自引率
15.10%
发文量
325
期刊介绍:
IEEE Transactions on Network and Service Management will publish (online only) peerreviewed archival quality papers that advance the state-of-the-art and practical applications of network and service management. Theoretical research contributions (presenting new concepts and techniques) and applied contributions (reporting on experiences and experiments with actual systems) will be encouraged. These transactions will focus on the key technical issues related to: Management Models, Architectures and Frameworks; Service Provisioning, Reliability and Quality Assurance; Management Functions; Enabling Technologies; Information and Communication Models; Policies; Applications and Case Studies; Emerging Technologies and Standards.
 求助内容:
求助内容: 应助结果提醒方式:
应助结果提醒方式:


