Cyber Attacks Prevention Toward Prosumer-Based EV Charging Stations: An Edge-Assisted Federated Prototype Knowledge Distillation Approach
IF 5.4
2区 计算机科学
Q1 COMPUTER SCIENCE, INFORMATION SYSTEMS
IEEE Transactions on Network and Service Management
Pub Date : 2024-12-16
DOI:10.1109/TNSM.2024.3517621
引用次数: 0
Abstract
In this paper, cyber-attack prevention for the prosumer-based electric vehicle (EV) charging stations (EVCSs) is investigated, which covers two aspects: 1) cyber-attack detection on prosumers’ network traffic (NT) data, and 2) cyber-attack intervention. To establish an effective prevention mechanism, several challenges need to be tackled, for instance, the NT data per prosumer may be non-independent and identically distributed (non-IID), and the boundary between benign and malicious traffic becomes blurred. To this end, we propose an edge-assisted federated prototype knowledge distillation (E-FPKD) approach, where each client is deployed on a dedicated local edge server (DLES) and can report its availability for joining the federated learning (FL) process. Prior to the E-FPKD approach, to enhance accuracy, the Pearson Correlation Coefficient is adopted for feature selection. Regarding the proposed E-FPKD approach, we integrate the knowledge distillation and prototype aggregation technique into FL to deal with the non-IID challenge. To address the boundary issue, instead of directly calculating the distance between benign and malicious traffic, we consider maximizing the overall detection correctness of all prosumers (ODC), which can mitigate the computational cost compared with the former way. After detection, a rule-based method will be triggered at each DLES for cyber-attack intervention. Experimental analysis demonstrates that the proposed E-FPKD can achieve the largest ODC on NSL-KDD, UNSW-NB15, and IoTID20 datasets in both binary and multi-class classification, compared with baselines. For instance, the ODC for IoTID20 obtained via the proposed method is separately 0.3782% and 4.4471% greater than FedProto and FedAU in multi-class classification.针对产消型电动汽车充电站的网络攻击预防:一种边缘辅助联邦原型知识蒸馏方法
本文对产消型电动汽车充电站的网络攻击防范进行了研究,主要包括两个方面:产消型网络流量数据的网络攻击检测和网络攻击干预。为了建立有效的防御机制,需要解决以下几个问题:每个产消者的NT数据可能是非独立和同分布的(non-IID),良性和恶意流量之间的界限变得模糊。为此,我们提出了一种边缘辅助联邦原型知识蒸馏(E-FPKD)方法,其中每个客户端部署在专用的本地边缘服务器(dle)上,并可以报告其加入联邦学习(FL)过程的可用性。在E-FPKD方法之前,为了提高准确性,采用Pearson相关系数进行特征选择。对于所提出的E-FPKD方法,我们将知识蒸馏和原型聚合技术集成到FL中,以应对非iid挑战。为了解决边界问题,我们不直接计算良性流量和恶意流量之间的距离,而是考虑最大化所有产消者(ODC)的总体检测正确性,与前一种方法相比,这可以降低计算成本。检测后,在每个dle触发基于规则的方法进行网络攻击干预。实验分析表明,与基线相比,所提出的E-FPKD在NSL-KDD、UNSW-NB15和IoTID20数据集上的二元和多类分类ODC最大。例如,在多类分类中,通过本文方法获得的IoTID20的ODC分别比FedProto和FedAU高0.3782%和4.4471%。
本文章由计算机程序翻译,如有差异,请以英文原文为准。
求助全文
约1分钟内获得全文
求助全文
来源期刊
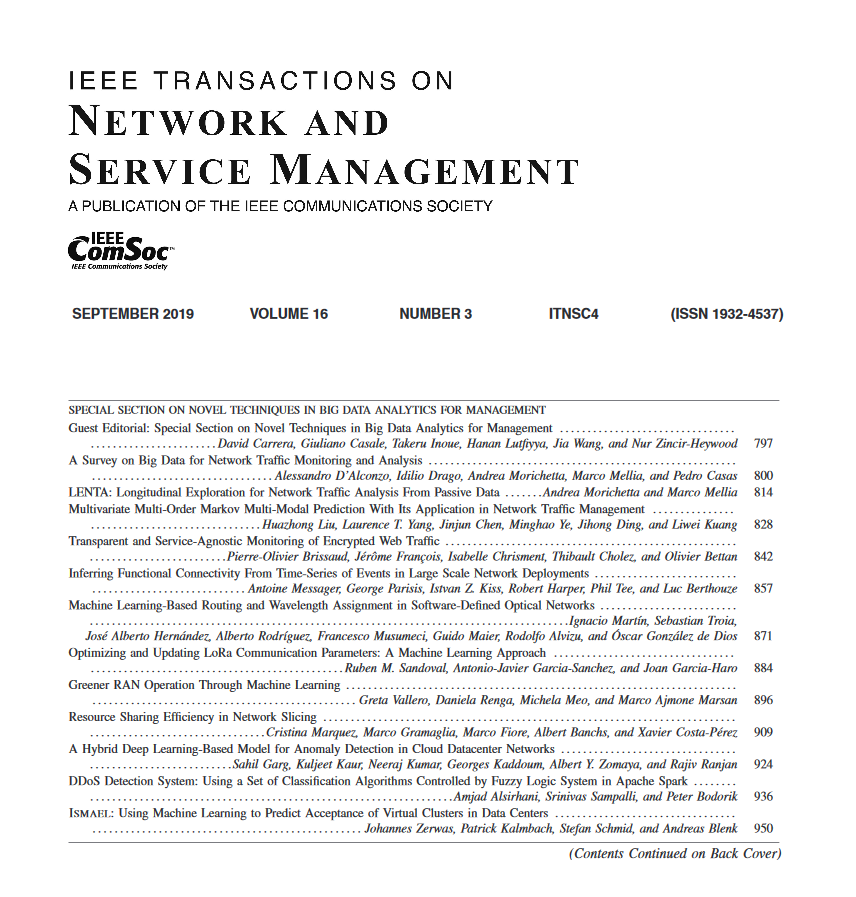
IEEE Transactions on Network and Service Management
Computer Science-Computer Networks and Communications
CiteScore
9.30
自引率
15.10%
发文量
325
期刊介绍:
IEEE Transactions on Network and Service Management will publish (online only) peerreviewed archival quality papers that advance the state-of-the-art and practical applications of network and service management. Theoretical research contributions (presenting new concepts and techniques) and applied contributions (reporting on experiences and experiments with actual systems) will be encouraged. These transactions will focus on the key technical issues related to: Management Models, Architectures and Frameworks; Service Provisioning, Reliability and Quality Assurance; Management Functions; Enabling Technologies; Information and Communication Models; Policies; Applications and Case Studies; Emerging Technologies and Standards.
 求助内容:
求助内容: 应助结果提醒方式:
应助结果提醒方式:


