Dynamic Policy Decision/Enforcement Security Zoning Through Stochastic Games and Meta Learning
IF 4.7
2区 计算机科学
Q1 COMPUTER SCIENCE, INFORMATION SYSTEMS
IEEE Transactions on Network and Service Management
Pub Date : 2024-10-16
DOI:10.1109/TNSM.2024.3481662
引用次数: 0
Abstract
Securing Next Generation Networks (NGNs) remains a prominent topic of discussion in academia and industries alike, driven by the rapid evolution of cyber attacks. As these attacks become increasingly complex and dynamic, it is crucial to develop sophisticated security strategies with automated dynamic policy enforcement. In this paper, we propose a security strategy based on the zero-trust model, incorporating dynamic policy decisions through the utilization of stochastic games and Reinforcement Learning (RL). Our approach involves the development of an attack and defense strategy evolution model, specifically tailored to combat cyber attacks in NGNs. To achieve this, we employ RL techniques to update and adapt dynamic policies. To train the agents, we utilize the Generalized Proximal Policy Optimization with sample reuse (GePPO) algorithm, including its modified version, GePPO-ML, which incorporates meta-learning to initialize the agent’s policy and parameters. Additionally, we employ the Sample Dropout PPO with meta-learning (SDPPO-ML), a modified version of the SD-PPO algorithm, to train the agents. To evaluate the performance of these algorithms, we conduct a comparative analysis against the REINFORCE and PPO algorithms. The results illustrate the superior performance of both GePPO-ML and SDPPO-ML when compared to these baseline algorithms, with GePPO-ML exhibiting the best performance.求助全文
约1分钟内获得全文
求助全文
来源期刊
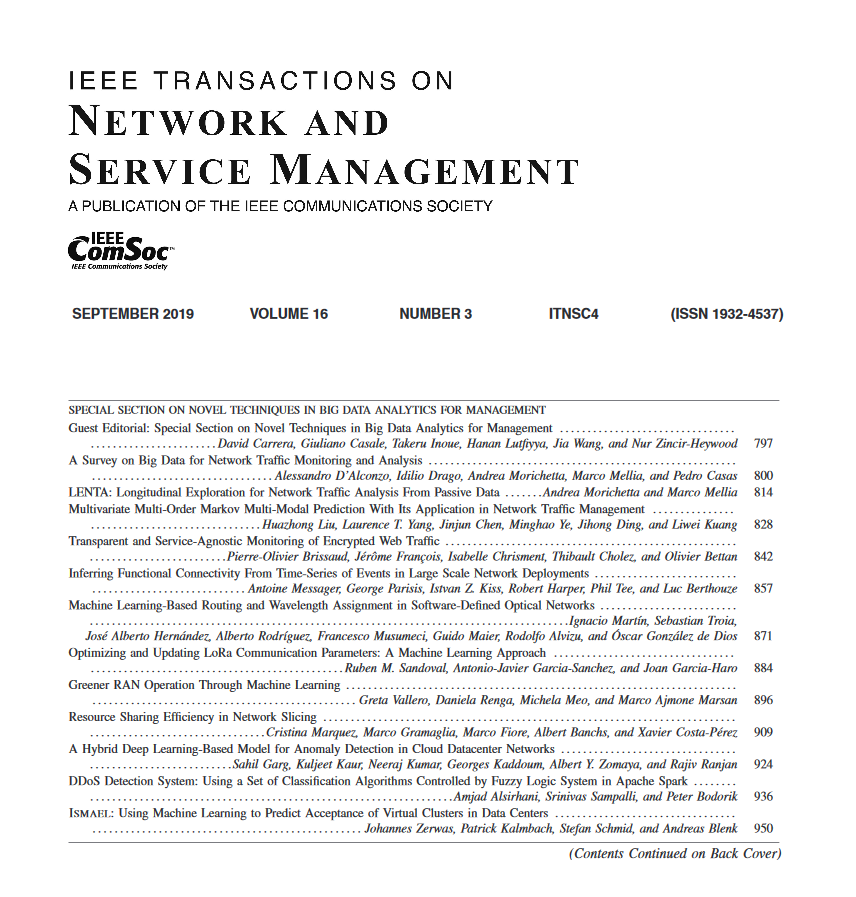
IEEE Transactions on Network and Service Management
Computer Science-Computer Networks and Communications
CiteScore
9.30
自引率
15.10%
发文量
325
期刊介绍:
IEEE Transactions on Network and Service Management will publish (online only) peerreviewed archival quality papers that advance the state-of-the-art and practical applications of network and service management. Theoretical research contributions (presenting new concepts and techniques) and applied contributions (reporting on experiences and experiments with actual systems) will be encouraged. These transactions will focus on the key technical issues related to: Management Models, Architectures and Frameworks; Service Provisioning, Reliability and Quality Assurance; Management Functions; Enabling Technologies; Information and Communication Models; Policies; Applications and Case Studies; Emerging Technologies and Standards.
 求助内容:
求助内容: 应助结果提醒方式:
应助结果提醒方式:


