Security and Privacy Issues and Solutions for UAVs in B5G Networks: A Review
IF 4.7
2区 计算机科学
Q1 COMPUTER SCIENCE, INFORMATION SYSTEMS
IEEE Transactions on Network and Service Management
Pub Date : 2024-10-28
DOI:10.1109/TNSM.2024.3487265
引用次数: 0
Abstract
Unmanned aerial vehicles (UAVs) in beyond 5G (B5G) are crucial for revolutionizing various industries, including surveillance, agriculture, and logistics, by enabling high-speed data transfer, ultra-low latency communication, and ultra-reliable connectivity. However, integrating UAVs into B5G networks poses various security and privacy concerns. These risks encompass the possibility of unauthorized access, breaches of data, and cyber-physical attacks which jeopardize the integrity, confidentiality, and availability of UAV operations. Moreover, UAVs in B5G networks are also at high risk from the application of machine learning (ML)-based attacks by exploiting vulnerabilities in ML models, leading to adversarial manipulation, data poisoning and model evasion techniques, which can compromise the integrity of UAV operations, lead to navigation errors, and expose sensitive data collected by UAVs. Considering the aforementioned security and privacy concerns, this review article presents emerging security and privacy solutions for UAVs in B5G networks. Firstly, We introduce the essential background of integrating UAVs into B5G networks and discuss the advantages and security challenges which the emerging integrated network architecture have. Then, we proceed to analyze and examine the security and privacy landscape by including threats and requirements of UAVs in B5G networks. Based on these threats and requirements, solutions from physical layer security (PLS), blockchain (BC), federated learning (FL) and post-quantum cryptography (PQC) are discussed and explored in details. Moreover, potential future research directions are discussed in details as open research issues.求助全文
约1分钟内获得全文
求助全文
来源期刊
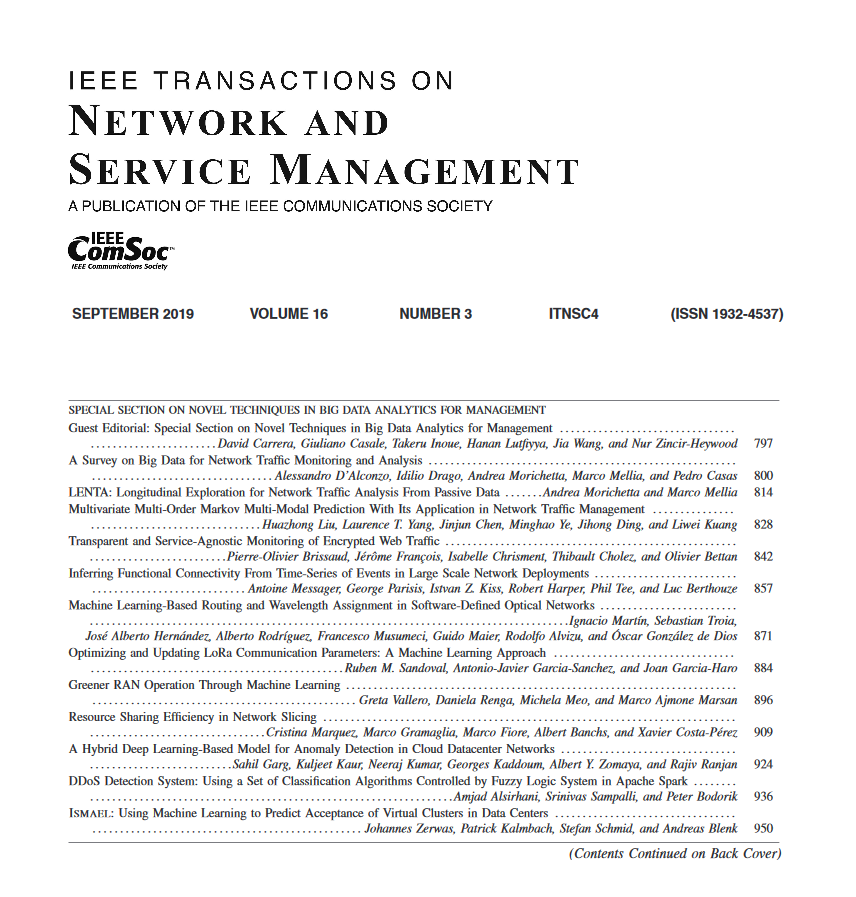
IEEE Transactions on Network and Service Management
Computer Science-Computer Networks and Communications
CiteScore
9.30
自引率
15.10%
发文量
325
期刊介绍:
IEEE Transactions on Network and Service Management will publish (online only) peerreviewed archival quality papers that advance the state-of-the-art and practical applications of network and service management. Theoretical research contributions (presenting new concepts and techniques) and applied contributions (reporting on experiences and experiments with actual systems) will be encouraged. These transactions will focus on the key technical issues related to: Management Models, Architectures and Frameworks; Service Provisioning, Reliability and Quality Assurance; Management Functions; Enabling Technologies; Information and Communication Models; Policies; Applications and Case Studies; Emerging Technologies and Standards.
 求助内容:
求助内容: 应助结果提醒方式:
应助结果提醒方式:


