Security Control Grid for Optimized Cyber Defense Planning
IF 4.7
2区 计算机科学
Q1 COMPUTER SCIENCE, INFORMATION SYSTEMS
IEEE Transactions on Network and Service Management
Pub Date : 2024-10-30
DOI:10.1109/TNSM.2024.3488011
引用次数: 0
Abstract
Cybersecurity controls are essential for ensuring information confidentiality, integrity, and availability. However, selecting the most effective controls to maximize return on investment (RoI) in cyber defense is a complex task involving numerous factors such as vulnerabilities, threat prioritization, and budget constraints. This paper introduces an innovative model and optimization techniques to select cybersecurity controls (CSC) for optimal risk mitigation, balancing residual risk, budget, and resiliency requirements. Our approach features the Security Control Grid (SCG) model, which automatically determines the necessary controls based on their security functions (Identify, Protect, Detect, Respond, and Recover), strategic placement within the cyber environment, and effectiveness at different stages of the attack kill chain. We formulate cybersecurity control decision-making as a multidimensional optimization problem, solving it using Satisfiability Modulo Theories (SMT). Additionally, we integrate a domain-specific language model that links CSCs with Common Vulnerabilities and Exposures (CVEs). This approach is implemented in the SCG solver tool, which generates scalable and robust CSC deployment plans that optimize cybersecurity RoI and maintain acceptable residual risk for large-scale enterprises.求助全文
约1分钟内获得全文
求助全文
来源期刊
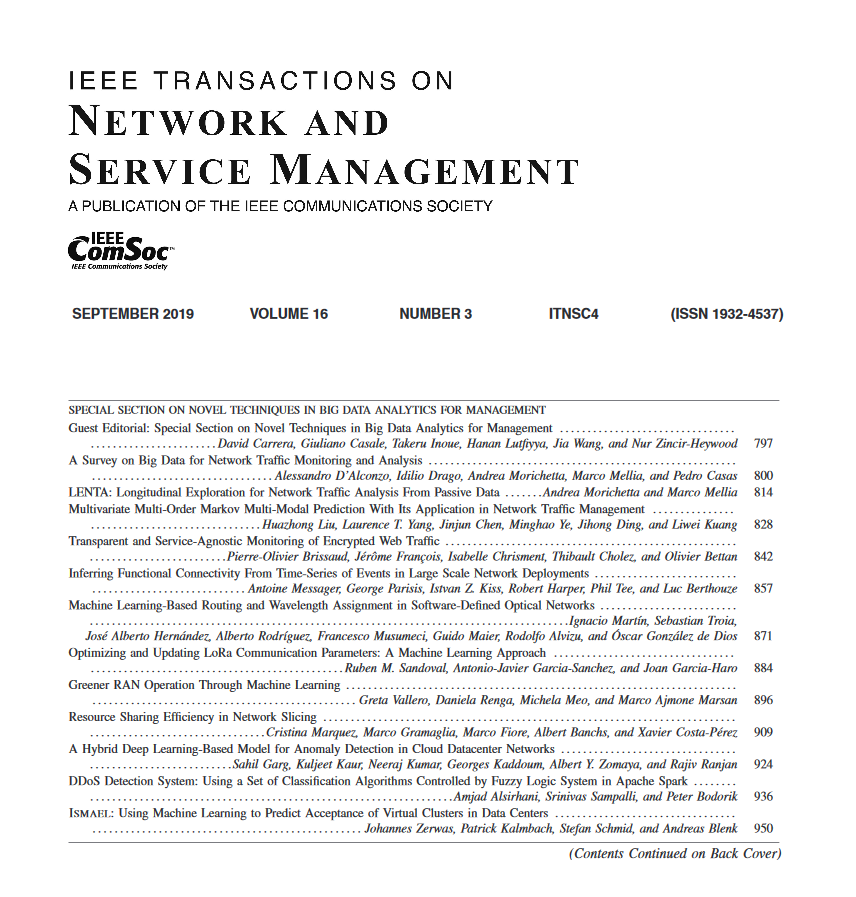
IEEE Transactions on Network and Service Management
Computer Science-Computer Networks and Communications
CiteScore
9.30
自引率
15.10%
发文量
325
期刊介绍:
IEEE Transactions on Network and Service Management will publish (online only) peerreviewed archival quality papers that advance the state-of-the-art and practical applications of network and service management. Theoretical research contributions (presenting new concepts and techniques) and applied contributions (reporting on experiences and experiments with actual systems) will be encouraged. These transactions will focus on the key technical issues related to: Management Models, Architectures and Frameworks; Service Provisioning, Reliability and Quality Assurance; Management Functions; Enabling Technologies; Information and Communication Models; Policies; Applications and Case Studies; Emerging Technologies and Standards.
 求助内容:
求助内容: 应助结果提醒方式:
应助结果提醒方式:


