Is There a DDoS?: System+Application Variable Monitoring to Ascertain the Attack Presence
IF 4.7
2区 计算机科学
Q1 COMPUTER SCIENCE, INFORMATION SYSTEMS
IEEE Transactions on Network and Service Management
Pub Date : 2024-08-29
DOI:10.1109/TNSM.2024.3451613
引用次数: 0
Abstract
The state of the art has numerous contributions which focus on combating the DDoS attacks. We argue that the mitigation methods are only useful if the victim service or the mitigation method can ascertain the presence of a DDoS attack. In many of the past solutions, the authors decide the presence of DDoS using quick and dirty checks. However, precise mechanisms are still needed so that the accurate decisions about DDoS mitigation can be made. In this work, we propose a method for detecting the presence of DDoS attacks using system variables available at the server or victim server operating system. To achieve this, we propose a machine learning based detection model in which there are three steps involved. In the first step, we monitored 14 different systems and application variables/ characteristics with and without a variety of DDoS attacks. In the second step, we trained machine learning model with monitored data of all the selected variables. In the final step, our approach uses the artificial neural network (ANN) and random forest (RF) based approaches to detect the presence of DDoS attacks. Our presence identification approach gives a detection accuracy of 88%-95% for massive attacks, 65%-77% for mixed traffic having a mixture of low-rate attack and benign requests, 58%-60% for flashcrowd, 76%-81% for mixed traffic having a mixture of massive attack and benign traffic and 58%-64% for low rate attacks with a detection time of 4-5 seconds.有 DDoS 吗?系统+应用变量监控以确定攻击是否存在
目前的技术状态有许多专注于对抗DDoS攻击的贡献。我们认为,只有当受害者服务或缓解方法能够确定DDoS攻击的存在时,缓解方法才有用。在过去的许多解决方案中,作者使用快速和肮脏的检查来确定DDoS的存在。但是,仍然需要精确的机制,以便能够做出有关DDoS缓解的准确决策。在这项工作中,我们提出了一种使用服务器或受害服务器操作系统上可用的系统变量来检测DDoS攻击存在的方法。为了实现这一点,我们提出了一个基于机器学习的检测模型,其中涉及三个步骤。在第一步中,我们监控了14个不同的系统和应用程序变量/特征,有和没有各种DDoS攻击。在第二步中,我们使用所有选定变量的监控数据训练机器学习模型。在最后一步中,我们的方法使用基于人工神经网络(ANN)和随机森林(RF)的方法来检测DDoS攻击的存在。我们的存在识别方法对大规模攻击的检测准确率为88%-95%,对低速率攻击和良性请求混合流量的检测准确率为65%-77%,对flashcrowd的检测准确率为58%-60%,对大规模攻击和良性流量混合流量的检测准确率为76%-81%,对低速率攻击的检测准确率为58%-64%,检测时间为4-5秒。
本文章由计算机程序翻译,如有差异,请以英文原文为准。
求助全文
约1分钟内获得全文
求助全文
来源期刊
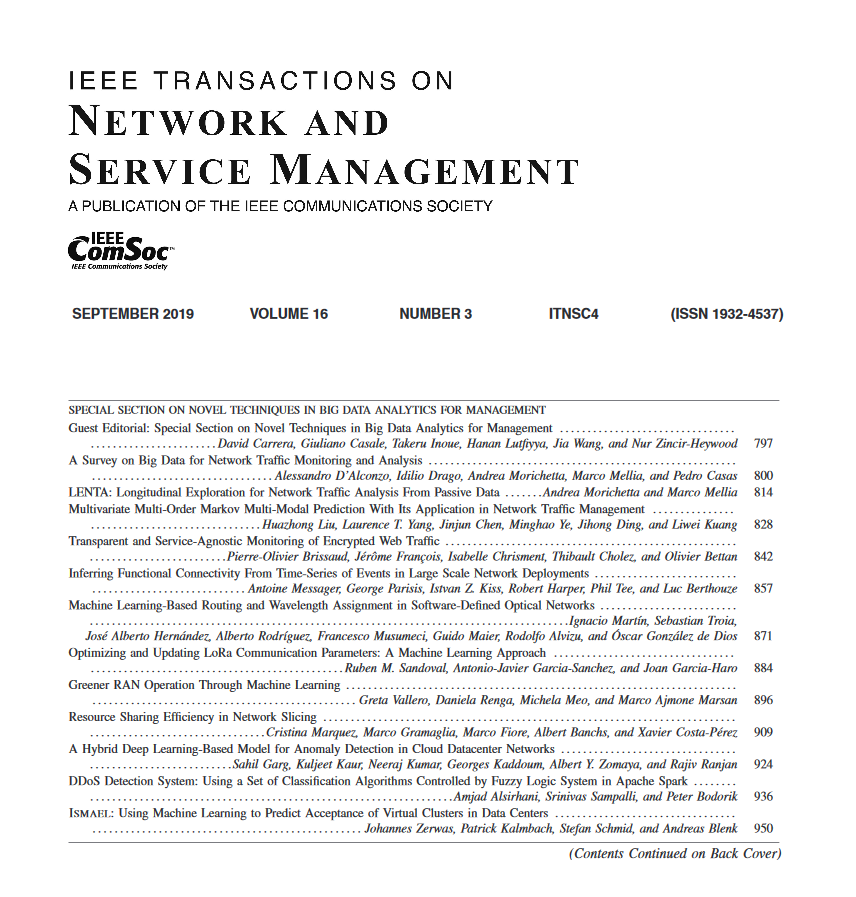
IEEE Transactions on Network and Service Management
Computer Science-Computer Networks and Communications
CiteScore
9.30
自引率
15.10%
发文量
325
期刊介绍:
IEEE Transactions on Network and Service Management will publish (online only) peerreviewed archival quality papers that advance the state-of-the-art and practical applications of network and service management. Theoretical research contributions (presenting new concepts and techniques) and applied contributions (reporting on experiences and experiments with actual systems) will be encouraged. These transactions will focus on the key technical issues related to: Management Models, Architectures and Frameworks; Service Provisioning, Reliability and Quality Assurance; Management Functions; Enabling Technologies; Information and Communication Models; Policies; Applications and Case Studies; Emerging Technologies and Standards.
 求助内容:
求助内容: 应助结果提醒方式:
应助结果提醒方式:


