FAPM: A Fake Amplification Phenomenon Monitor to Filter DRDoS Attacks With P4 Data Plane
IF 4.7
2区 计算机科学
Q1 COMPUTER SCIENCE, INFORMATION SYSTEMS
IEEE Transactions on Network and Service Management
Pub Date : 2024-08-26
DOI:10.1109/TNSM.2024.3449889
引用次数: 0
Abstract
Distributed Reflection Denial-of-Service (DRDoS) attacks have caused significant destructive effects by virtue of emerging protocol vulnerabilities and amplification advantages, and their intensity is increasing. The emergence of programmable data plane supporting line-rate forwarding provides a new opportunity for fine-grained and efficient attack detection. This paper proposed a light-weight DRDoS attack detection and mitigation system called FAPM, which is deployed at the victim end with the intention of detecting the amplification behavior caused by the attack. It places the work of collecting and calculating reflection features on the data plane operated by “latter window assisting former window” mechanism, and arranges complex identification and regulation logic on the control plane. This approach avoids the hardware constraints of the programmable switch while leveraging their per-packet processing capability. Also, it reduces communication traffic significantly through feature compression and state transitions. Experiments show that FAPM has (1) fast response capability within seconds (2) a memory footprint at the KB level and communication overhead of 1 Kbps, and (3) good robustness.FAPM:利用 P4 数据平面过滤 DRDoS 攻击的假放大现象监控器
分布式反射拒绝服务(Distributed Reflection Denial-of-Service,简称ddos)攻击利用新出现的协议漏洞和放大优势,造成了严重的破坏性影响,攻击强度不断增强。支持线速率转发的可编程数据平面的出现,为细粒度、高效的攻击检测提供了新的契机。本文提出了一种轻量级的DRDoS攻击检测与缓解系统FAPM,该系统部署在受害者端,目的是检测由攻击引起的放大行为。将收集和计算反射特征的工作放在“后窗辅助前窗”机制操作的数据平面上,将复杂的识别和调节逻辑安排在控制平面上。这种方法避免了可编程交换机的硬件限制,同时利用了它们的逐包处理能力。此外,它还通过特征压缩和状态转换显著减少了通信流量。实验表明,FAPM具有(1)秒级快速响应能力(2)KB级内存占用和1 Kbps的通信开销(3)良好的鲁棒性。
本文章由计算机程序翻译,如有差异,请以英文原文为准。
求助全文
约1分钟内获得全文
求助全文
来源期刊
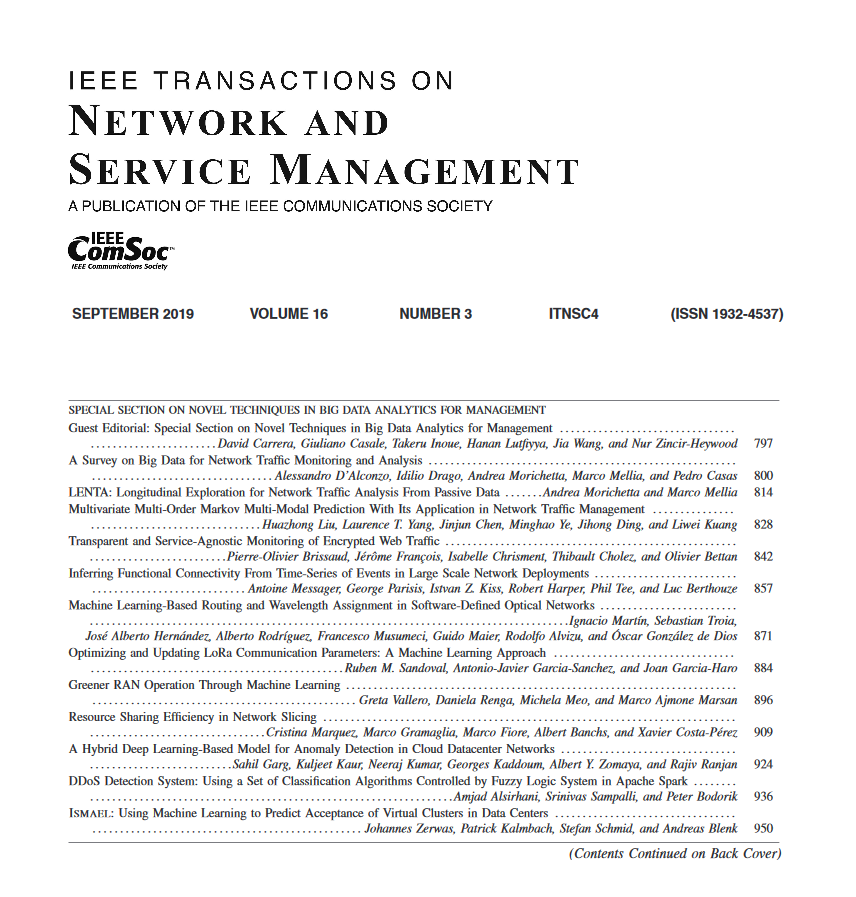
IEEE Transactions on Network and Service Management
Computer Science-Computer Networks and Communications
CiteScore
9.30
自引率
15.10%
发文量
325
期刊介绍:
IEEE Transactions on Network and Service Management will publish (online only) peerreviewed archival quality papers that advance the state-of-the-art and practical applications of network and service management. Theoretical research contributions (presenting new concepts and techniques) and applied contributions (reporting on experiences and experiments with actual systems) will be encouraged. These transactions will focus on the key technical issues related to: Management Models, Architectures and Frameworks; Service Provisioning, Reliability and Quality Assurance; Management Functions; Enabling Technologies; Information and Communication Models; Policies; Applications and Case Studies; Emerging Technologies and Standards.
 求助内容:
求助内容: 应助结果提醒方式:
应助结果提醒方式:


