离散调制连续可变量子密钥分发的可信源噪声模型
IF 4.4
2区 物理与天体物理
Q2 PHYSICS, APPLIED
引用次数: 0
摘要
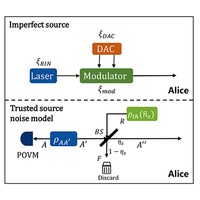
离散调制连续可变量子密钥分配提供了一种实用的解决方案,大大简化了实验程序,同时与经典光通信保持了稳健的结合。理论分析逐步验证了这一协议的全面安全性,为实际实验铺平了道路。然而,实际应用中不完美的信号源会带来噪声。传统的方法是假设窃听者可以控制所有的源噪声,这就高估了窃听者的能力,低估了秘钥率。源噪声的某些部分是固有的,窃听者无法控制,因此可以将其视为可信噪声。我们专门为离散调制协议定制了可信噪声模型,并相应地升级了安全分析。仿真结果表明,这种方法成功地减轻了不完美信号源对系统性能的负面影响,同时保持了协议的安全性。此外,我们的方法还可与可信探测器噪声模型结合使用,有效降低实验装置中源噪声和探测器噪声的影响。这对离散-调制-连续-变量-量子密钥分发系统的实际部署是一个有意义的贡献。本文章由计算机程序翻译,如有差异,请以英文原文为准。
Trusted-source-noise model of discrete-modulated continuous-variable quantum key distribution
Discrete-modulated continuous-variable quantum key distribution offers a pragmatic solution, greatly simplifying experimental procedures, while retaining robust integration with classical optical communication. Theoretical analyses have progressively validated the comprehensive security of this protocol, paving the way for practical experimentation. However, imperfect sources in practical implementations introduce noise. The traditional approach is to assume that eavesdroppers can control all of the source noise, which overestimates the ability of eavesdroppers and underestimates the secret-key rate. Some parts of source noise are intrinsic and cannot be manipulated by the eavesdropper, so they can be seen as trusted noise. We tailor a trusted-noise model specifically for the discrete-modulated protocol and upgrade the security analysis accordingly. Simulation results demonstrate that this approach successfully mitigates the negative impact of an imperfect source on system performance, while maintaining security of the protocol. Furthermore, our method can be used in conjunction with a trusted-detector-noise model, effectively reducing the influence of both source noise and detector noise in the experimental setup. This is a meaningful contribution to the practical deployment of discrete-modulated-continuous-variable-quantum-key-distribution systems.
求助全文
通过发布文献求助,成功后即可免费获取论文全文。
去求助
来源期刊

Physical Review Applied
PHYSICS, APPLIED-
CiteScore
7.80
自引率
8.70%
发文量
760
审稿时长
2.5 months
期刊介绍:
Physical Review Applied (PRApplied) publishes high-quality papers that bridge the gap between engineering and physics, and between current and future technologies. PRApplied welcomes papers from both the engineering and physics communities, in academia and industry.
PRApplied focuses on topics including:
Biophysics, bioelectronics, and biomedical engineering,
Device physics,
Electronics,
Technology to harvest, store, and transmit energy, focusing on renewable energy technologies,
Geophysics and space science,
Industrial physics,
Magnetism and spintronics,
Metamaterials,
Microfluidics,
Nonlinear dynamics and pattern formation in natural or manufactured systems,
Nanoscience and nanotechnology,
Optics, optoelectronics, photonics, and photonic devices,
Quantum information processing, both algorithms and hardware,
Soft matter physics, including granular and complex fluids and active matter.
 求助内容:
求助内容: 应助结果提醒方式:
应助结果提醒方式:


