HiRAM:分级风险评估模型及其在云中的工业物联网实施
IF 1.2
4区 计算机科学
Q3 COMPUTER SCIENCE, SOFTWARE ENGINEERING
引用次数: 0
摘要
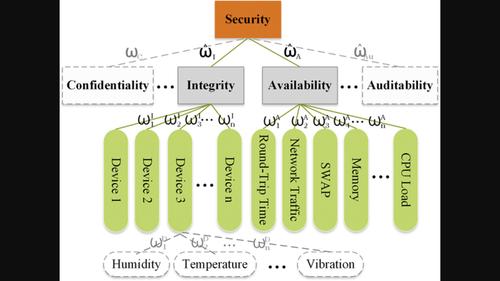
智能控制过程的趋势已将物联网(IoT)和云计算技术引入工厂。物联网设备可以感知数据并将其发送到云端,以便在工厂进行进一步分析。因此,在工业网络-物理系统中流动的此类有价值数据的数量逐渐增加。为工业物联网(IIoT)量身定制风险评估系统至关重要,特别是对于处理工业物联网数据流的云平台。在本研究中,我们利用层次分析法(ahp)并提出了工业物联网云平台的层次风险评估模型(HiRAM)。所提出的模型允许平台自我评估其安全状态。此外,基于HiRAM的模块化响应式风险评估系统(称为HiRAM - RAS)在现实世界的IIoT云平台上实现和评估。我们将HiRAM - RAS部署到一个示例应用程序中,并介绍了实际的部署过程。然后,我们通过注入不同程度的错误和发起分布式拒绝服务(DDoS)攻击来估计HiRAM - RAS的实用性。结果显示了HiRAM评估的完整性和可用性得分的变化。本文章由计算机程序翻译,如有差异,请以英文原文为准。
HiRAM: A hierarchical risk assessment model and its implementation for an industrial Internet of Things in the cloud
The trend towards intelligent control processes has introduced the Internet of Things (IoT) and cloud computing technologies to factories. IoT devices can sense data and send it to a cloud for further analysis in a factory. Consequently, the quantity of such valuable data flowing in an industrial cyber‐physical system has gradually increased. Tailoring a risk assessment system for Industrial IoT (IIoT) is essential, particularly for a cloud platform that handles the IIoT data flow. In this study, we leverage analytic hierarchy processes (AHPs) and propose Hierarchical Risk Assessment Model (HiRAM) for an IIoT cloud platform. The proposed model allows the platform to self‐evaluate its security status. Furthermore, a modular and responsive Risk Assessment System based on HiRAM, called HiRAM‐RAS, is realized and evaluated in a real‐world IIoT cloud platform. We deploy HiRAM‐RAS to a sample application and introduce the practical deployment procedures. We then estimate the practicality of the HiRAM‐RAS by injecting different degrees of errors and launching Distributed denial‐of‐service (DDoS) attacks. The results demonstrate the changes in integrity and availability scores evaluated by HiRAM.
求助全文
通过发布文献求助,成功后即可免费获取论文全文。
去求助
来源期刊

Software Testing Verification & Reliability
工程技术-计算机:软件工程
CiteScore
3.70
自引率
0.00%
发文量
34
审稿时长
>12 weeks
期刊介绍:
The journal is the premier outlet for research results on the subjects of testing, verification and reliability. Readers will find useful research on issues pertaining to building better software and evaluating it.
The journal is unique in its emphasis on theoretical foundations and applications to real-world software development. The balance of theory, empirical work, and practical applications provide readers with better techniques for testing, verifying and improving the reliability of software.
The journal targets researchers, practitioners, educators and students that have a vested interest in results generated by high-quality testing, verification and reliability modeling and evaluation of software. Topics of special interest include, but are not limited to:
-New criteria for software testing and verification
-Application of existing software testing and verification techniques to new types of software, including web applications, web services, embedded software, aspect-oriented software, and software architectures
-Model based testing
-Formal verification techniques such as model-checking
-Comparison of testing and verification techniques
-Measurement of and metrics for testing, verification and reliability
-Industrial experience with cutting edge techniques
-Descriptions and evaluations of commercial and open-source software testing tools
-Reliability modeling, measurement and application
-Testing and verification of software security
-Automated test data generation
-Process issues and methods
-Non-functional testing
 求助内容:
求助内容: 应助结果提醒方式:
应助结果提醒方式:


