i-DarkVec:用于暗网流量分析的增量嵌入
IF 4.1
3区 计算机科学
Q2 COMPUTER SCIENCE, INFORMATION SYSTEMS
引用次数: 3
摘要
暗网是监听到达没有服务的IP地址的流量的探测器。到达暗网的流量是由互联网扫描仪、僵尸网络以及可能配置错误的主机的操作造成的。暗网流量的这种特殊性质使暗网成为发现恶意在线活动的宝贵工具,例如识别机器人或扫描仪执行的协调行动。然而,暗网观察到的大量数据包和来源使得很难提取有意义的见解,需要可扩展的工具来自动识别和分组具有类似行为的来源。我们在这里介绍i-DarkVec,这是一种学习暗网流量有意义表示的方法。i-DarkVec利用自然语言处理技术(例如Word2Verc)来捕捉扫描仪或机器人启动协调动作时出现的共现模式。与NLP问题一样,使用i-DarkVec学习的嵌入能够在暗网流量上执行一些新的机器学习任务,例如识别参与类似活动的发送者集群。我们对i-DarkVec进行了广泛的测试,并在一个使用真实暗网的案例研究中探索了它的设计空间。我们表明,通过对服务的正确定义,学习到的嵌入可以用于(i)解决分类问题,将未知来源的IP地址与正确的协调参与者类别相关联,以及(ii)自动识别执行类似攻击和扫描的先前未知来源的集群,从而简化安全分析师的工作。i-DarkVec利用了一种新颖的增量嵌入学习方法,该方法可扩展且对流量变化具有鲁棒性,适用于动态和大规模场景。本文章由计算机程序翻译,如有差异,请以英文原文为准。
i-DarkVec: Incremental Embeddings for Darknet Traffic Analysis
Darknets are probes listening to traffic reaching IP addresses that host no services. Traffic reaching a darknet results from the actions of internet scanners, botnets, and possibly misconfigured hosts. Such peculiar nature of the darknet traffic makes darknets a valuable instrument to discover malicious online activities, e.g., identifying coordinated actions performed by bots or scanners. However, the massive amount of packets and sources that darknets observe makes it hard to extract meaningful insights, calling for scalable tools to automatically identify and group sources that share similar behaviour. We here present i-DarkVec, a methodology to learn meaningful representations of Darknet traffic. i-DarkVec leverages Natural Language Processing techniques (e.g., Word2Vec) to capture the co-occurrence patterns that emerge when scanners or bots launch coordinated actions. As in NLP problems, the embeddings learned with i-DarkVec enable several new machine learning tasks on the darknet traffic, such as identifying clusters of senders engaged in similar activities. We extensively test i-DarkVec and explore its design space in a case study using real darknets. We show that with a proper definition of services, the learned embeddings can be used to (i) solve the classification problem to associate unknown sources’ IP addresses to the correct classes of coordinated actors and (ii) automatically identify clusters of previously unknown sources performing similar attacks and scans, easing the security analyst’s job. i-DarkVec leverages a novel incremental embedding learning approach that is scalable and robust to traffic changes, making it applicable to dynamic and large-scale scenarios.
求助全文
通过发布文献求助,成功后即可免费获取论文全文。
去求助
来源期刊
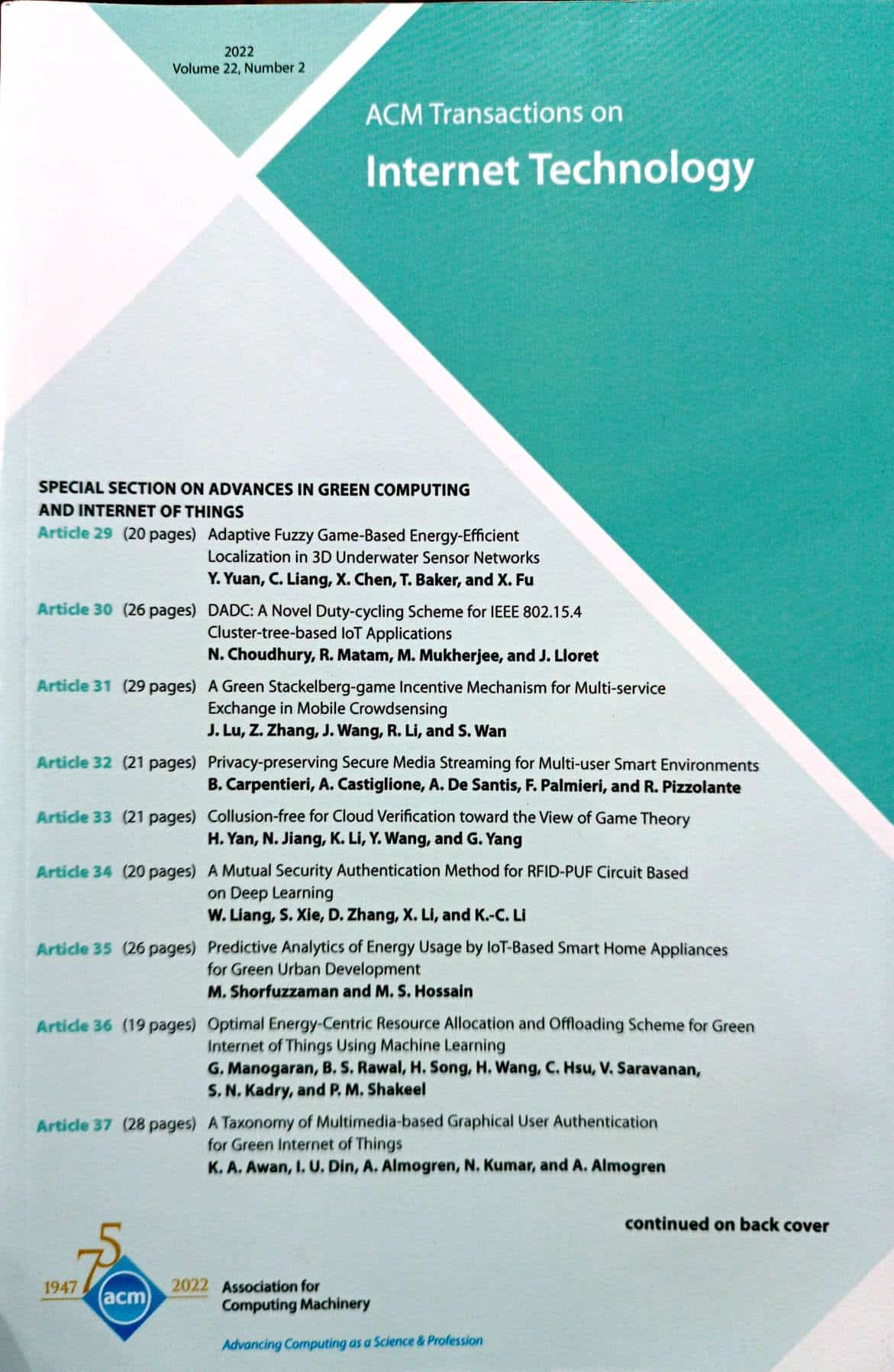
ACM Transactions on Internet Technology
工程技术-计算机:软件工程
CiteScore
10.30
自引率
1.90%
发文量
137
审稿时长
>12 weeks
期刊介绍:
ACM Transactions on Internet Technology (TOIT) brings together many computing disciplines including computer software engineering, computer programming languages, middleware, database management, security, knowledge discovery and data mining, networking and distributed systems, communications, performance and scalability etc. TOIT will cover the results and roles of the individual disciplines and the relationshipsamong them.
 求助内容:
求助内容: 应助结果提醒方式:
应助结果提醒方式:


