伪装网:安全的图像外包机密模型训练在云
IF 4.1
3区 计算机科学
Q2 COMPUTER SCIENCE, INFORMATION SYSTEMS
引用次数: 0
摘要
大量的训练数据和昂贵的模型调整是图像深度学习的标准特征。因此,数据所有者经常利用云资源开发大规模复杂模型,这也引发了隐私问题。现有的用于训练深度神经网络(dnn)的加密解决方案过于昂贵,不能有效地利用云GPU资源,并且给客户端预处理带来了很大的负担。本文介绍了一种图像伪装方法:DisguisedNets,它允许用户安全地将图像外包到云,并实现机密、高效的基于gpu的模型训练。DisguisedNets使用图像块化、块级随机排列和块级安全转换的新颖组合:随机多维投影(RMT)或AES像素级加密(AES)来转换训练数据。用户可以使用现有的DNN训练方法和GPU资源,而无需对伪装图像的训练模型进行任何修改。我们在多级威胁模型下分析和评估了这些方法,并将它们与另一种类似的方法instahide进行了比较。我们还表明,包括DisguisedNets和InstaHide在内的图像伪装方法可以有效地保护模型免受针对模型的攻击。本文章由计算机程序翻译,如有差异,请以英文原文为准。
DisguisedNets: Secure Image Outsourcing for Confidential Model Training in Clouds
Large training data and expensive model tweaking are standard features of deep learning with images. As a result, data owners often utilize cloud resources to develop large-scale complex models, which also raises privacy concerns. Existing cryptographic solutions for training deep neural networks (DNNs) are too expensive, cannot effectively utilize cloud GPU resources, and also put a significant burden on client-side pre-processing. This article presents an image disguising approach: DisguisedNets, which allows users to securely outsource images to the cloud and enables confidential, efficient GPU-based model training. DisguisedNets uses a novel combination of image blocktization, block-level random permutation, and block-level secure transformations: random multidimensional projection (RMT) or AES pixel-level encryption (AES) to transform training data. Users can use existing DNN training methods and GPU resources without any modification to training models with disguised images. We have analyzed and evaluated the methods under a multi-level threat model and compared them with another similar method—InstaHide. We also show that the image disguising approach, including both DisguisedNets and InstaHide, can effectively protect models from model-targeted attacks.
求助全文
通过发布文献求助,成功后即可免费获取论文全文。
去求助
来源期刊
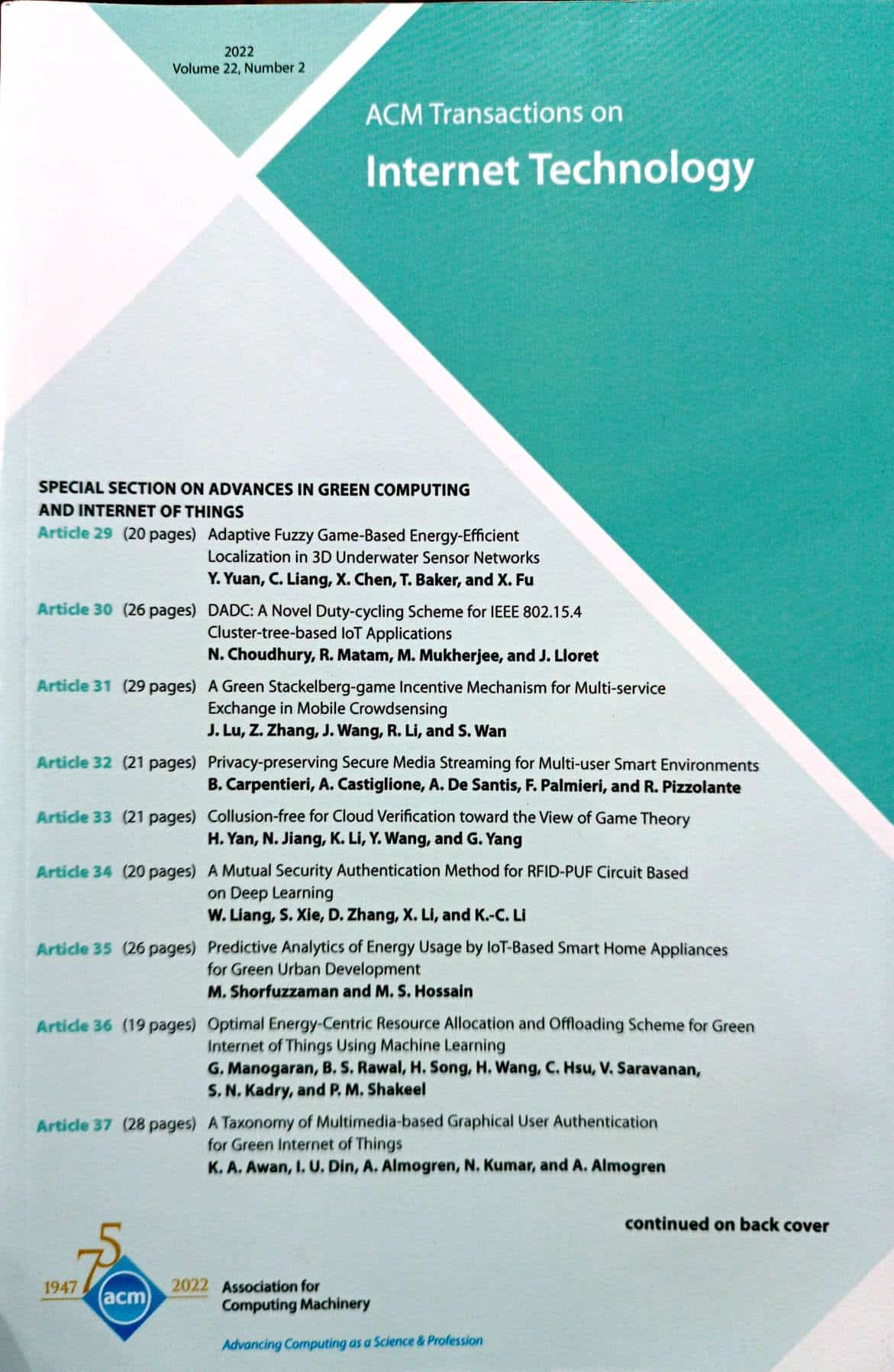
ACM Transactions on Internet Technology
工程技术-计算机:软件工程
CiteScore
10.30
自引率
1.90%
发文量
137
审稿时长
>12 weeks
期刊介绍:
ACM Transactions on Internet Technology (TOIT) brings together many computing disciplines including computer software engineering, computer programming languages, middleware, database management, security, knowledge discovery and data mining, networking and distributed systems, communications, performance and scalability etc. TOIT will cover the results and roles of the individual disciplines and the relationshipsamong them.
 求助内容:
求助内容: 应助结果提醒方式:
应助结果提醒方式:


