基于RoBERTa和稀疏自编码器的恶意URL检测新方法
IF 3.7
2区 计算机科学
Q2 COMPUTER SCIENCE, INFORMATION SYSTEMS
Journal of Information Security and Applications
Pub Date : 2025-09-03
DOI:10.1016/j.jisa.2025.104214
引用次数: 0
摘要
检测请求中的恶意url是阻止Web威胁的有效方法。目前检测恶意url的方法主要依赖于有监督机器学习算法来构建分类模型,因此需要高质量的训练数据。而且这些方法在检测恶意样本时也存在局限性,导致在遇到未知异常时假阴性率较高。提出了一种基于RoBERTa和稀疏自编码器的恶意url异常检测方法。该方法最初涉及对URL示例进行预处理。随后,利用RoBERTa从url中提取特征,并将其转换为特征向量。最后利用稀疏自编码器对恶意样本进行检测。在模型训练过程中,只使用良性样本作为输入。它使稀疏自编码器能够有效地重构良性样本的特征来识别恶意样本。在CSIC2010和PRDREQ组成的数据集上对该方法进行了测试。实验结果表明,该检测模型的准确率为0.9921,召回率为0.9863,F1得分为0.9887,优于所有基线方法。本文章由计算机程序翻译,如有差异,请以英文原文为准。
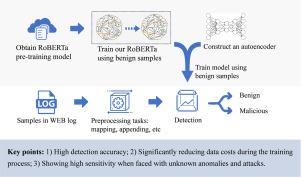
A novel approach for malicious URL detection using RoBERTa and sparse autoencoder
Detecting malicious URLs within requests is an effective method for blocking Web threats. Current methods for detecting malicious URLs mainly rely on supervised machine learning algorithms to construct classification models, which consequently demand high-quality training data. And these methods also have limitations in detecting malicious samples, resulting in a high false negative rate when encountering unknown anomalies. This paper proposes an anomaly detection method based on RoBERTa and sparse autoencoder for detecting malicious URLs. This method initially involves preprocessing the URL samples. Subsequently, RoBERTa is used to extract features from URLs and converts them into feature vectors. Sparse autoencoder is utilized to detect malicious samples ultimately. During the model training process, only benign samples are used as input. It enables sparse autoencoder to effectively reconstruct the characteristics of benign samples to identify malicious ones. This method was tested on the dataset composed of CSIC2010 and PRDREQ. The experimental results show that the detection model achieves an accuracy of 0.9921, a recall of 0.9863, and an F1 score of 0.9887, outperforming all baseline methods.
求助全文
通过发布文献求助,成功后即可免费获取论文全文。
去求助
来源期刊

Journal of Information Security and Applications
Computer Science-Computer Networks and Communications
CiteScore
10.90
自引率
5.40%
发文量
206
审稿时长
56 days
期刊介绍:
Journal of Information Security and Applications (JISA) focuses on the original research and practice-driven applications with relevance to information security and applications. JISA provides a common linkage between a vibrant scientific and research community and industry professionals by offering a clear view on modern problems and challenges in information security, as well as identifying promising scientific and "best-practice" solutions. JISA issues offer a balance between original research work and innovative industrial approaches by internationally renowned information security experts and researchers.
 求助内容:
求助内容: 应助结果提醒方式:
应助结果提醒方式:


