阴影之网调查恶意软件滥用互联网服务
IF 4.8
2区 计算机科学
Q1 COMPUTER SCIENCE, INFORMATION SYSTEMS
引用次数: 0
摘要
互联网网络和云服务经常被恶意软件滥用,但这种滥用的广度尚未得到彻底调查。在这项工作中,我们利用网络威胁联盟(CTA)的数据对这种滥用现象进行了定量研究,36 家安全厂商在该联盟中共享威胁情报。我们分析了从 2020 年 1 月到 2023 年 12 月的 4 年间收集的 CTA 数据,其中包括超过 10 亿个网络安全观察结果,我们从中提取了 770 万个与恶意软件相关的 URL 和 180 万个域。我们通过主动测量对该数据集进行补充,定期尝试下载最近报告的 33876 个恶意 URL 所指向的内容。我们研究了以下问题。恶意软件滥用互联网服务的普遍程度如何?滥用互联网服务的域名有何不同?滥用互联网服务的目的是什么? 恶意资源的活跃时间有多长?其中,我们发现了影响 22K 个互联网服务域的广泛滥用现象,互联网服务在很大程度上是为传播恶意软件而滥用的,而且互联网服务中的恶意内容比恶意域上的恶意内容保持活跃的时间更长。本文章由计算机程序翻译,如有差异,请以英文原文为准。
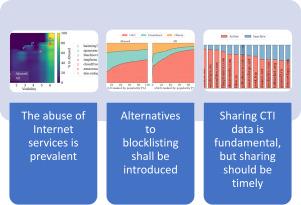
Web of shadows: Investigating malware abuse of internet services
Internet Web and cloud services are routinely abused by malware, but the breadth of this abuse has not been thoroughly investigated. In this work, we quantitatively investigate this abuse by leveraging data from the Cyber Threat Alliance (CTA), where 36 security vendors share threat intelligence. We analyze CTA data collected over 4 years from January 2020 until December 2023 comprising over one billion cyber-security observations from where we extract 7.7M URLs and 1.8M domains related to malware. We complement this dataset with an active measurement where we periodically attempt to download the content pointed out by 33,876 recently reported malicious URLs. We investigate the following questions. How generalized is malware abuse of Internet services? How do domains of abused Internet services differ? For what purpose are Internet services abused? and How long do malicious resources remain active? Among others, we uncover a broad abuse affecting 22K domains of Internet services, that Internet services are largely abused for enabling malware distribution, and that malicious content in Internet services remains active longer than on malicious domains.
求助全文
通过发布文献求助,成功后即可免费获取论文全文。
去求助
来源期刊

Computers & Security
工程技术-计算机:信息系统
CiteScore
12.40
自引率
7.10%
发文量
365
审稿时长
10.7 months
期刊介绍:
Computers & Security is the most respected technical journal in the IT security field. With its high-profile editorial board and informative regular features and columns, the journal is essential reading for IT security professionals around the world.
Computers & Security provides you with a unique blend of leading edge research and sound practical management advice. It is aimed at the professional involved with computer security, audit, control and data integrity in all sectors - industry, commerce and academia. Recognized worldwide as THE primary source of reference for applied research and technical expertise it is your first step to fully secure systems.
 求助内容:
求助内容: 应助结果提醒方式:
应助结果提醒方式:


