基于多因素身份验证、视觉密码学和隐写术的移动设备用户数据保护方法
IF 0.6
Q4 AUTOMATION & CONTROL SYSTEMS
引用次数: 0
摘要
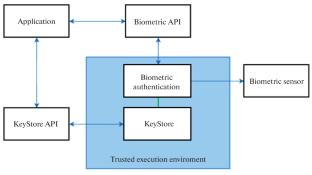
本文提出了一种方法来保护运行安卓操作系统的移动设备上存储的用户个人数据,该方法结合了多因素身份验证、秘密共享、可视化加密和隐写术,还使用了操作系统的内置安全功能。即使移动设备和相关的远程存储(服务器)都遭到破坏,它也能确保个人数据的机密性。本文章由计算机程序翻译,如有差异,请以英文原文为准。
Approach for Protecting Mobile Device User’s Data Based on Multifactor Authentication, Visual Cryptography, and Steganography
An approach is proposed to protect user’s personal data stored on mobile devices running the Android OS, which combines multifactor authentication, secret sharing, visual cryptography, and steganography; and it also uses the built-in security features of the operating system. It ensures the confidentiality of personal data even if both the mobile device and the related remote storage (server) are compromised.
求助全文
通过发布文献求助,成功后即可免费获取论文全文。
去求助
来源期刊

AUTOMATIC CONTROL AND COMPUTER SCIENCES
AUTOMATION & CONTROL SYSTEMS-
CiteScore
1.70
自引率
22.20%
发文量
47
期刊介绍:
Automatic Control and Computer Sciences is a peer reviewed journal that publishes articles on• Control systems, cyber-physical system, real-time systems, robotics, smart sensors, embedded intelligence • Network information technologies, information security, statistical methods of data processing, distributed artificial intelligence, complex systems modeling, knowledge representation, processing and management • Signal and image processing, machine learning, machine perception, computer vision
 求助内容:
求助内容: 应助结果提醒方式:
应助结果提醒方式:


