基于代码的高效电子取证一次性盲签名方案
IF 2.6
4区 计算机科学
Q3 COMPUTER SCIENCE, INFORMATION SYSTEMS
引用次数: 0
摘要
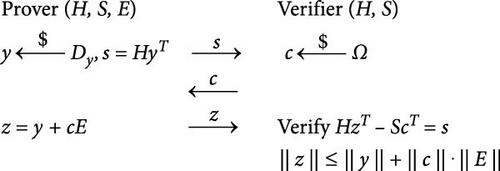
我们提出了一种基于编码理论的一次性盲签名方案,该方案在 SHMWW 协议的基础上进行了改进。通过增加两个盲因子,保护了用户的匿名性。分析证明,该方案是安全的,满足完整性、盲性和一次不可伪造性的要求。在 128 位安全等级下,我们的方案可以实现 2.1 kB 的签名长度。实验结果表明,我们的方案具有较短的签名长度和较高的执行效率。我们的方案还可应用于车联网交通事故的电子取证,保护用户隐私。本文章由计算机程序翻译,如有差异,请以英文原文为准。

An Efficient Code-Based One-Time Blind Signature Scheme for Electronic Forensics
We propose a one-time blind signature scheme based on coding theory, which is improved on the basis of the SHMWW protocol. By adding two blinding factors, the anonymity of users is protected. The analysis proves that the scheme is secure and meets the requirements of completeness, blindness, and one-more unforgeability. Under the 128-bit security level, our scheme can achieve a signature length of 2.1 kB. The experimental results show that our scheme has a short signature length and high execution efficiency. Our scheme can also be applied to electronic forensics of traffic accidents on the Internet of Vehicles, which can protect users’ privacy.
求助全文
通过发布文献求助,成功后即可免费获取论文全文。
去求助
来源期刊

IET Information Security
工程技术-计算机:理论方法
CiteScore
3.80
自引率
7.10%
发文量
47
审稿时长
8.6 months
期刊介绍:
IET Information Security publishes original research papers in the following areas of information security and cryptography. Submitting authors should specify clearly in their covering statement the area into which their paper falls.
Scope:
Access Control and Database Security
Ad-Hoc Network Aspects
Anonymity and E-Voting
Authentication
Block Ciphers and Hash Functions
Blockchain, Bitcoin (Technical aspects only)
Broadcast Encryption and Traitor Tracing
Combinatorial Aspects
Covert Channels and Information Flow
Critical Infrastructures
Cryptanalysis
Dependability
Digital Rights Management
Digital Signature Schemes
Digital Steganography
Economic Aspects of Information Security
Elliptic Curve Cryptography and Number Theory
Embedded Systems Aspects
Embedded Systems Security and Forensics
Financial Cryptography
Firewall Security
Formal Methods and Security Verification
Human Aspects
Information Warfare and Survivability
Intrusion Detection
Java and XML Security
Key Distribution
Key Management
Malware
Multi-Party Computation and Threshold Cryptography
Peer-to-peer Security
PKIs
Public-Key and Hybrid Encryption
Quantum Cryptography
Risks of using Computers
Robust Networks
Secret Sharing
Secure Electronic Commerce
Software Obfuscation
Stream Ciphers
Trust Models
Watermarking and Fingerprinting
Special Issues. Current Call for Papers:
Security on Mobile and IoT devices - https://digital-library.theiet.org/files/IET_IFS_SMID_CFP.pdf
 求助内容:
求助内容: 应助结果提醒方式:
应助结果提醒方式:


