使用机器学习算法检测恶意安装文件的特点
IF 0.5
Q4 AUTOMATION & CONTROL SYSTEMS
引用次数: 0
摘要
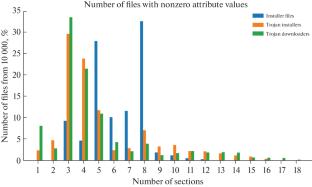
摘要 本文研究了使用机器学习方法检测与木马安装程序和下载程序类型有关的恶意安装文件的可能性。本文对适用于解决这一问题的机器学习算法进行了比较分析:奈夫贝叶斯分类器(NBC)、随机森林和 C4.5 算法。机器学习模型使用 Weka 软件开发。突出了合法程序和木马程序安装文件的最重要属性。本文章由计算机程序翻译,如有差异,请以英文原文为准。

Features of Detecting Malicious Installation Files Using Machine Learning Algorithms
This paper presents a study of the possibility of using machine learning methods to detect malicious installation files related to the type of Trojan installers and downloaders. A comparative analysis of machine learning algorithms applicable for the solution of this problem is provided: the naive Bayes classifier (NBC), random forest, and C4.5 algorithm. Machine learning models are developed using the Weka software. The most significant attributes of installation files of legitimate and Trojan programs are highlighted.
求助全文
通过发布文献求助,成功后即可免费获取论文全文。
去求助
来源期刊

AUTOMATIC CONTROL AND COMPUTER SCIENCES
AUTOMATION & CONTROL SYSTEMS-
CiteScore
1.70
自引率
22.20%
发文量
47
期刊介绍:
Automatic Control and Computer Sciences is a peer reviewed journal that publishes articles on• Control systems, cyber-physical system, real-time systems, robotics, smart sensors, embedded intelligence • Network information technologies, information security, statistical methods of data processing, distributed artificial intelligence, complex systems modeling, knowledge representation, processing and management • Signal and image processing, machine learning, machine perception, computer vision
 求助内容:
求助内容: 应助结果提醒方式:
应助结果提醒方式:


