后量子密码学协议同源图结构研究
IF 0.6
Q4 AUTOMATION & CONTROL SYSTEMS
引用次数: 0
摘要
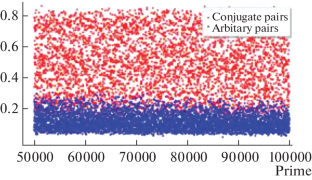
摘要超星曲线的同源图是后量子加密算法中很有前途的数学结构之一。然而,最近报道的对 SIDH 协议的攻击[1]表明,在应用于实际协议时,需要对等值图进行更详细的研究。在本研究中,我们分析了度数为 \(\ell > 2\) 的同源图的结构,并考虑了一种特殊类型的顶点集,对该顶点集的攻击适用于重建图中的路径[7]。本文章由计算机程序翻译,如有差异,请以英文原文为准。
Investigation of the Structure of the Isogeny Graph for Postquantum Cryptography Protocols
The isogeny graphs of supersingular curves are one of the promising mathematical structures in postquantum cryptography algorithms. However, the recently reported attack on the SIDH protocol [1] demonstrates that the isogeny graphs require a more detailed investigation when applied to real protocols. In this study, we analyze the structure of the graphs of isogenies of degree \(\ell > 2\) and consider the set of vertices of a special type to which an attack on reconstruction of the path in the graph is applicable [7].
求助全文
通过发布文献求助,成功后即可免费获取论文全文。
去求助
来源期刊

AUTOMATIC CONTROL AND COMPUTER SCIENCES
AUTOMATION & CONTROL SYSTEMS-
CiteScore
1.70
自引率
22.20%
发文量
47
期刊介绍:
Automatic Control and Computer Sciences is a peer reviewed journal that publishes articles on• Control systems, cyber-physical system, real-time systems, robotics, smart sensors, embedded intelligence • Network information technologies, information security, statistical methods of data processing, distributed artificial intelligence, complex systems modeling, knowledge representation, processing and management • Signal and image processing, machine learning, machine perception, computer vision
 求助内容:
求助内容: 应助结果提醒方式:
应助结果提醒方式:


