On the security of ‘an ultra-lightweight and secure scheme for communications of smart metres and neighbourhood gateways by utilisation of an ARM Cortex-M microcontroller’
IF 1.3
4区 计算机科学
Q3 COMPUTER SCIENCE, INFORMATION SYSTEMS
引用次数: 2
Abstract
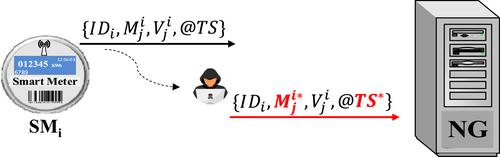
In 2018, Abbasinezhad-Mood and Nikooghadam (IEEE Transaction on Smart Grid, pp 6194–6205, 9(6), 2018) proposed an ultra-lightweight secure scheme for neighbourhood area network () communications in smart grid. They have claimed that their protocol is secure against all known attacks in environment by providing informal security analysis besides a formal analysis which was done by using an automatic verification tool. However, by performing several attacks, this study shows that their scheme has serious security flaws. After performing each attack, lightweight countermeasures is proposed for securing their protocol against that attack.
关于“利用ARM Cortex-M微控制器实现智能电表和邻里网关通信的超轻量级安全方案”的安全性
2018年,Abbasinezhad Mood和Nikooghadam(IEEE智能电网交易,第6194–6205页,9(6),2018)提出了一种用于智能电网中邻域网络(N A N$\boldsymbol{N}\boldsymbol{A}\bold symbol{N}$)通信的超轻量级安全方案。他们声称,他们的协议除了通过使用自动验证工具。然而,通过多次攻击,本研究表明他们的方案存在严重的安全缺陷。在执行每一次攻击之后,都会提出轻量级对策来保护他们的协议免受该攻击。
本文章由计算机程序翻译,如有差异,请以英文原文为准。
求助全文
约1分钟内获得全文
求助全文
来源期刊

IET Information Security
工程技术-计算机:理论方法
CiteScore
3.80
自引率
7.10%
发文量
47
审稿时长
8.6 months
期刊介绍:
IET Information Security publishes original research papers in the following areas of information security and cryptography. Submitting authors should specify clearly in their covering statement the area into which their paper falls.
Scope:
Access Control and Database Security
Ad-Hoc Network Aspects
Anonymity and E-Voting
Authentication
Block Ciphers and Hash Functions
Blockchain, Bitcoin (Technical aspects only)
Broadcast Encryption and Traitor Tracing
Combinatorial Aspects
Covert Channels and Information Flow
Critical Infrastructures
Cryptanalysis
Dependability
Digital Rights Management
Digital Signature Schemes
Digital Steganography
Economic Aspects of Information Security
Elliptic Curve Cryptography and Number Theory
Embedded Systems Aspects
Embedded Systems Security and Forensics
Financial Cryptography
Firewall Security
Formal Methods and Security Verification
Human Aspects
Information Warfare and Survivability
Intrusion Detection
Java and XML Security
Key Distribution
Key Management
Malware
Multi-Party Computation and Threshold Cryptography
Peer-to-peer Security
PKIs
Public-Key and Hybrid Encryption
Quantum Cryptography
Risks of using Computers
Robust Networks
Secret Sharing
Secure Electronic Commerce
Software Obfuscation
Stream Ciphers
Trust Models
Watermarking and Fingerprinting
Special Issues. Current Call for Papers:
Security on Mobile and IoT devices - https://digital-library.theiet.org/files/IET_IFS_SMID_CFP.pdf
 求助内容:
求助内容: 应助结果提醒方式:
应助结果提醒方式:


