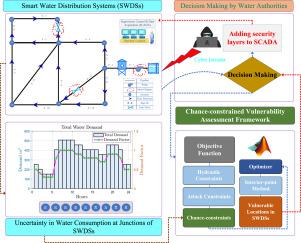
Chance-constrained vulnerability assessment of smart water distribution systems against stealthy false data injection attacks
Abstract
Smart water distribution systems (SWDSs) have not only enhanced the monitoring and control of the entire water infrastructure but have also jeopardized its security and resilience. The state-of-the-art examined the uncertainties in the water supply network to obtain optimal design parameters to ensure hydraulic integrity. However, the investigations of uncertainties in SWDSs from the cybersecurity perspective remain unexplored. To address this limitation, this paper utilizes a robust chance-constrained optimization strategy to scrutinize the vulnerable location of SWDSs against False Data Injection (FDI) attacks. This is achieved by factoring in the probabilistic behavior of water demand at junctions that can potentially facilitate stealthy FDI attacks on the hourly measurements of the pump’s flow rate. The proposed nonlinear model is validated with several case studies reflecting the real-world cyberattack consequences including cutoff water supply of the network, enhanced power consumption of the pump, and the undesirable pressure surge in the system at strategic locations of SWDSs. As a result of the studied cases, the cyberattack consequences on the entire water supply network are obtained while highlighting the threat-prone regions of the network. This paper contributes to embedding additional security layers to the existing water infrastructure at the vulnerable links and junctions.

 求助内容:
求助内容: 应助结果提醒方式:
应助结果提醒方式:


