Quantum Cryptography in 5G Networks: A Comprehensive Overview
IF 34.4
1区 计算机科学
Q1 COMPUTER SCIENCE, INFORMATION SYSTEMS
引用次数: 0
Abstract
Every attempt to access to the Internet through a Web browser, email sent, VPN connection, VoIP call, instant message or other use of telecommunications systems involves cryptographic techniques. The most commonly applied technique is asymmetric cryptography, which is generally executed in the background without the user even being aware. It establishes a cryptographic code based on the computational complexity of mathematical problems. However, this type of cryptography, which is widely used in today’s telecommunications systems, is under threat as electronics and computing rapidly develop. The development of fifth-generation cellular networks (5G) is gaining momentum, and given its wide field of application, security requires special attention. This is especially true faced with the development of quantum computers. One solution to this security challenge is to use more advanced techniques to establish cryptographic keys that are not susceptible to attack. An essential part of quantum cryptography, Quantum Key Distribution (QKD) uses the principles of quantum physics to establish and distribute symmetric cryptographic keys between two geographically distant users. QKD establishes information-theoretically secure cryptographic keys that are resistant to eavesdropping when they are created. In this paper, we survey the security challenges and approaches in 5G networks concerning network protocols, interfaces and management organizations. We begin by examining the fundamentals of QKD and discuss the creation of QKD networks and their applications. We then outline QKD network architecture and its components and standards, following with a summary of QKD and post-quantum key distribution techniques and approaches for its integration into existing security frameworks such as VPNs (IPsec and MACsec). We also discuss the requirements, architecture and methods for implementing the FPGA-based encryptors needed to execute cryptographic algorithms with security keys. We discuss the performance and technologies of post-quantum cryptography, and finally, examine reported 5G demonstrations which have used quantum technologies, highlighting future research directions.5G 网络中的量子密码学:全面概述
通过网络浏览器、发送电子邮件、VPN 连接、网络电话、即时信息或其他电信系统访问互联网的每一次尝试都涉及加密技术。最常用的技术是非对称加密技术,它通常在后台执行,用户根本不会察觉。它根据数学问题的计算复杂性建立加密代码。然而,随着电子技术和计算技术的飞速发展,这种广泛应用于当今电信系统的加密技术正受到威胁。第五代蜂窝网络(5G)的发展势头迅猛,鉴于其广泛的应用领域,安全性需要特别关注。面对量子计算机的发展,情况更是如此。应对这一安全挑战的一个解决方案是使用更先进的技术来建立不易受到攻击的加密密钥。量子密钥分发(QKD)是量子密码学的重要组成部分,它利用量子物理学原理在两个地理位置遥远的用户之间建立和分发对称密码密钥。QKD 可建立信息理论上安全的加密密钥,这些密钥在创建时不会被窃听。在本文中,我们将探讨 5G 网络中有关网络协议、接口和管理组织的安全挑战和方法。我们首先研究了 QKD 的基本原理,并讨论了 QKD 网络的创建及其应用。然后,我们概述了 QKD 网络架构及其组件和标准,接着总结了 QKD 和后量子密钥分发技术以及将其集成到 VPN(IPsec 和 MACsec)等现有安全框架中的方法。我们还讨论了执行带有安全密钥的加密算法所需的基于 FPGA 的加密器的要求、架构和实施方法。我们讨论了后量子加密技术的性能和技术,最后研究了已报道的使用量子技术的 5G 演示,强调了未来的研究方向。
本文章由计算机程序翻译,如有差异,请以英文原文为准。
求助全文
约1分钟内获得全文
求助全文
来源期刊
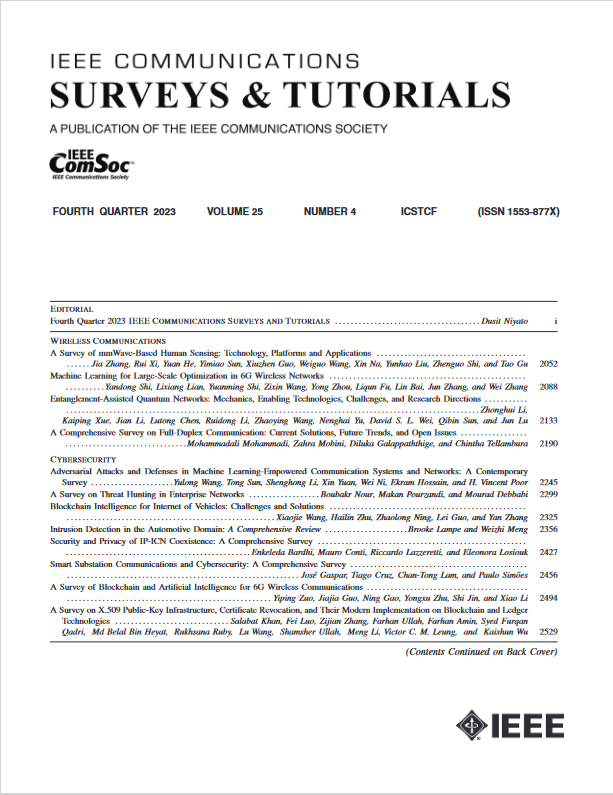
IEEE Communications Surveys and Tutorials
COMPUTER SCIENCE, INFORMATION SYSTEMS-TELECOMMUNICATIONS
CiteScore
80.20
自引率
2.50%
发文量
84
审稿时长
6 months
期刊介绍:
IEEE Communications Surveys & Tutorials is an online journal published by the IEEE Communications Society for tutorials and surveys covering all aspects of the communications field. Telecommunications technology is progressing at a rapid pace, and the IEEE Communications Society is committed to providing researchers and other professionals the information and tools to stay abreast. IEEE Communications Surveys and Tutorials focuses on integrating and adding understanding to the existing literature on communications, putting results in context. Whether searching for in-depth information about a familiar area or an introduction into a new area, IEEE Communications Surveys & Tutorials aims to be the premier source of peer-reviewed, comprehensive tutorials and surveys, and pointers to further sources. IEEE Communications Surveys & Tutorials publishes only articles exclusively written for IEEE Communications Surveys & Tutorials and go through a rigorous review process before their publication in the quarterly issues.
A tutorial article in the IEEE Communications Surveys & Tutorials should be designed to help the reader to become familiar with and learn something specific about a chosen topic. In contrast, the term survey, as applied here, is defined to mean a survey of the literature. A survey article in IEEE Communications Surveys & Tutorials should provide a comprehensive review of developments in a selected area, covering its development from its inception to its current state and beyond, and illustrating its development through liberal citations from the literature. Both tutorials and surveys should be tutorial in nature and should be written in a style comprehensible to readers outside the specialty of the article.
 求助内容:
求助内容: 应助结果提醒方式:
应助结果提醒方式:


